Kentik Blog
























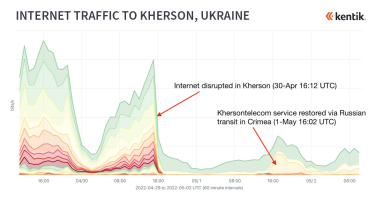
Since the beginning of June 2022, internet connectivity in the Russian-held Ukrainian city of Kherson has been rerouted through Crimea, the peninsula in southern Ukraine that has been occupied by Russia since March 2014. As I explain in this blog post, the rerouting of internet service in Kherson appears to parallel what took place following the Russian annexation of Crimea.
In this post we will show how to leverage Kentik Labs’ open source project ktranslate to bring network observability into the Sumo Logic platform.
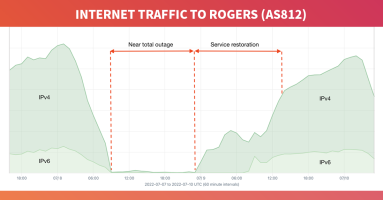
On July 8, 2022, Canadian telecommunications giant Rogers Communications suffered a catastrophic outage taking down nearly all services for its 11 million customers in the largest internet outage in Canadian history. We dig into the outage and debunk the notion that it was caused by the withdrawal of BGP routes.
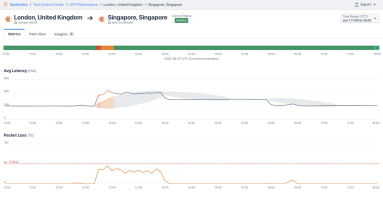
Investigating a user’s digital experience used to start with a help desk ticket, but with Kentik’s Synthetic Transaction Monitoring, you can proactively simulate and monitor a user’s interaction with any web application.
Kentik goes up the stack and launched Synthetic Transaction Monitoring (STM). Read this post to learn about enhancements to our synthetic testing capability and how to perform STM in Kentik.
The theme of augmenting the network engineer with diverse data and machine learning really took the main stage at the World of Solutions. Read Phil Gervasi’s recap.
On Tuesday, June 7, internet users in numerous countries from East Africa to the Middle East to South Asia experienced an hours-long degradation in service due to an outage at one of the internet’s most critical chokepoints: Egypt. In this blog post, we review some of the impacts as well as compare how this disruption affected connectivity within the three major public cloud providers.
By peeling back layers of your users’ interactions, you can investigate what’s going on in every aspect of their digital experience — from the network layer all the way to application.
With Kentik Synthetics, New Relic gains proactive insights about network performance and can ensure its customers have a reliable digital experience.
A critical milestone in any peering relationship is the business review; and when it comes to business reviews, it’s all about preparation. Learn how Kentik can help.