Get to the Bottom of Security Incidents
Never have to ask “what happened?”
Achieve lossless lookbacks with full fidelity data.
Understand timing, volume, and history of malicious traffic across the kill chain.
Close security gaps and understand bad actors.
Full-fidelity data retention
- Identify pre-breach reconnaissance.
- Understand historical data exfiltration/infiltration.
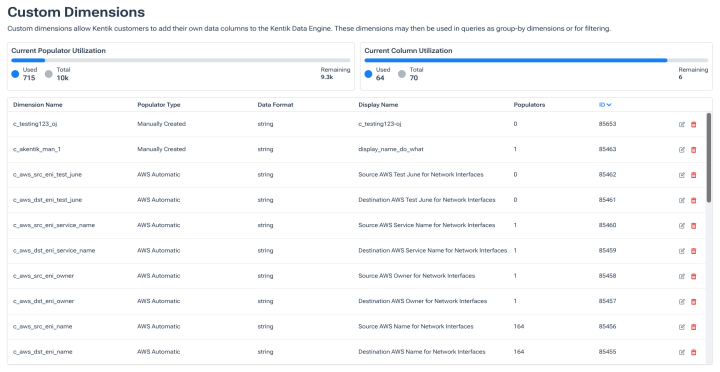
- Determine what accessed the network with global context, security, and business enriched metadata.
- Identify users with ID-enriched flow data.
Trace traffic inside and outside your networks
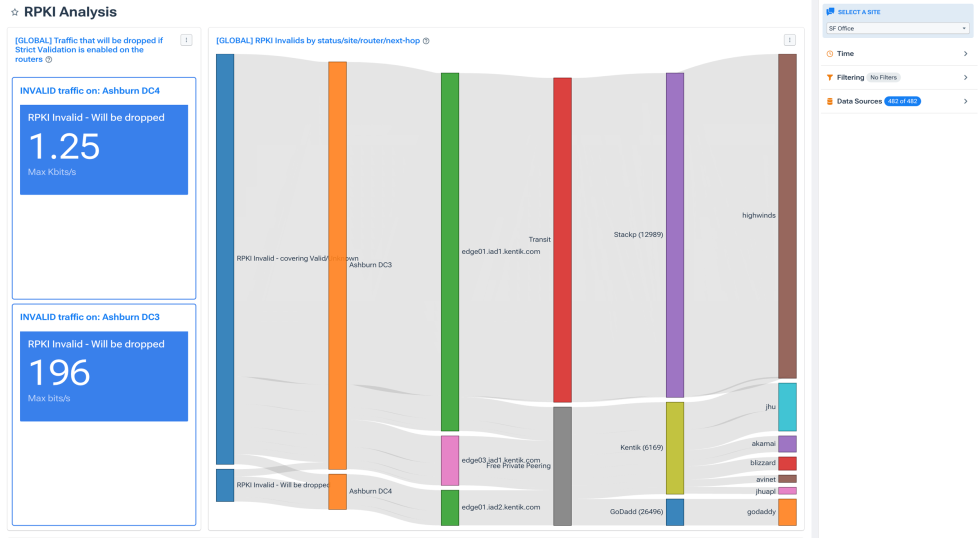
- Detect and alert on route hijacking incidents.
- Monitor and uncover unexpected traffic origins.
- Track changes in route propagation and identify BGP hijacks.
- Identify lateral movement and recon traffic.

Built for complex networks
- Analyze across data center, clouds, and containers.
- Audit traffic to and from the network to identify prohibited domains or geographies.
- Keep granular fidelity even during large spikes in traffic.

“With Kentik, we can pinpoint the source of suspicious traffic virtually in real time.”
Explore the platform
FAQs about Network Security Incident Investigation with Kentik
What kinds of security incidents can Kentik help investigate?
Kentik supports investigation of any incident with a network-traffic signature — including data exfiltration and theft, lateral movement after initial compromise, command-and-control communication, pre-breach reconnaissance, DDoS attacks, BGP hijacks and route leaks, DNS hijacking and cache poisoning, traffic to unsanctioned services or geographies, and shadow IT discovery. Because Kentik retains full-fidelity flow data alongside BGP, geographic, application, and business-context metadata, investigators can reconstruct what happened across data center, cloud, and internet boundaries even weeks or months after an event.
What’s the role of flow analytics in detecting data exfiltration?
Flow analytics surface the network-traffic patterns associated with data exfiltration — large outbound transfers to unusual destinations, sustained low-volume “low and slow” exfiltration to staging servers, DNS-based exfiltration patterns, and traffic to known malicious infrastructure or unsanctioned cloud services. Kentik supports this by retaining full-fidelity flow records enriched with geographic, AS path, threat intelligence, and business-context metadata at ingest. Security teams can run ad-hoc queries against historical flows to identify exfiltration patterns that match known techniques, baseline normal egress behavior to flag anomalies, and correlate suspicious outbound traffic with BGP and DNS context to confirm the destination.
What’s the best approach to detect lateral movement using network data?
Lateral movement leaves distinct east-west traffic signatures — communication between hosts that don’t normally interact, unusual protocol usage (RDP, SSH, SMB to new destinations), credential-probing patterns, and traffic that crosses segmentation boundaries it shouldn’t. Kentik supports lateral movement detection by capturing east-west flow data across data center, cloud, and Kubernetes environments (including pod-to-pod traffic via the Kentik Kappa agent), then enriching each record with business-context tags that identify which workloads and applications are communicating. Security teams use this to baseline normal east-west patterns and surface anomalies, identify violations of segmentation policy, and trace an attacker’s path through the network during incident response.
How does Kentik help identify the source of suspicious traffic?
Identifying the source of suspicious traffic requires multiple lenses on the same data: IP and ASN attribution, geographic source identification, traffic volume and protocol pattern analysis, and historical comparison to known threat actors. Kentik combines all of these by enriching each flow record at ingest with BGP-derived AS path information, GeoIP attribution, threat intelligence feeds, and user-defined business context. Investigators can pivot from a suspicious flow to the originating ASN or subnet, see what other traffic that source has generated historically, and correlate with BGP routing changes — getting from “something looks wrong” to “here’s exactly where it came from” in minutes.
How long does Kentik retain network flow data for forensic investigation?
Kentik retains unaggregated flow data for 120 days by default — substantially longer than most observability platforms (Datadog and similar tools typically retain 30 days). This matters for security investigation because breaches are often detected weeks or months after the initial compromise, and the investigator’s ability to reconstruct what happened depends on whether the underlying telemetry still exists. Longer retention is available for organizations with specific compliance or forensic requirements; the SaaS pricing model accommodates extended retention without the infrastructure cost of self-hosted log management.
How does Kentik help detect pre-breach reconnaissance?
Pre-breach reconnaissance has its own network signatures — port scanning patterns, probing of internet-facing services, DNS enumeration, unusual traffic to public-facing assets from anomalous sources. Kentik supports detection by baselining normal traffic patterns against critical assets, alerting on probing behavior that matches known reconnaissance techniques, and providing historical context to distinguish ongoing campaigns from one-off scans. The combination of full-fidelity flow data with ingest-time threat intelligence enrichment lets security teams catch reconnaissance early — before it escalates into successful exploitation.
How can I prioritize incident response using AI-driven insights?
AI-driven incident prioritization works best when the AI has access to rich, well-correlated telemetry rather than just alert metadata. Kentik AI Advisor reasons across flow data, BGP routing, synthetic monitoring, and device telemetry to investigate incidents end-to-end, surface evidence-backed verdicts, and recommend next steps — turning raw alerts into prioritized, actionable incidents. For network teams, this means fewer hours spent triaging false positives or hunting through dashboards, and more time spent on the incidents that actually matter. The AI explains its reasoning and shows the underlying evidence, so investigators can validate the assessment rather than accept it on faith.
What’s the difference between Kentik and dedicated NDR (Network Detection and Response) tools?
Network Detection and Response (NDR) tools focus specifically on detecting threats from network traffic — typically using deep packet inspection (DPI), behavioral analytics, and signature-based detection optimized for security use cases. Kentik is a network intelligence platform that includes strong security investigation capabilities (flow analytics, BGP hijack detection, exfiltration analysis, shadow IT discovery) but is not a dedicated NDR tool — it doesn’t perform DPI or maintain a signature library for known threats. Many security teams use Kentik alongside dedicated NDR platforms: NDR for real-time threat detection and signature matching, Kentik for network-wide forensic investigation, multi-cloud visibility, and the longer retention windows needed for breach reconstruction. For more on Kentik’s full security capabilities, see Kentik Network Security and Compliance.