How to Detect DDoS Attacks Using Flow Analytics: A Practical Guide
Flow-based DDoS detection uses metadata from network traffic — exported via protocols like NetFlow, IPFIX, and sFlow — to identify distributed denial-of-service attacks without inspecting packet payloads. Rather than deploying inline appliances at every network boundary, flow analytics processes telemetry that routers and switches are already generating, making it one of the most scalable and cost-effective approaches to DDoS detection available today. This guide explains how flow-based detection works in practice, how it compares to appliance-based approaches, and how modern platforms use it to automate DDoS response.
Detecting DDoS Attacks with Flow Analytics at a Glance
Flow-based DDoS detection works by analyzing traffic metadata exported from routers, switches, and cloud environments to spot attack patterns without inspecting packet payloads. Instead of looking inside packets, it looks for abnormal spikes in packets per second (pps), bits per second (bps), flows per second, destination ports, packet sizes, source distribution, and traffic concentration on specific IPs or prefixes.
In practice, this makes flow analytics especially effective for detecting volumetric floods, reflection and amplification attacks, SYN floods, and carpet-bombing attacks across large, distributed networks. Once an anomaly is detected, the same flow data can be used to classify the attack and trigger mitigation such as RTBH, BGP FlowSpec, or scrubbing-center diversion.
What Is Flow-Based DDoS Detection?
Flow-based DDoS detection is a network security method that identifies distributed denial-of-service attacks by analyzing network flow records — metadata about traffic patterns — rather than inspecting individual packet payloads. Using telemetry exported via protocols like NetFlow, IPFIX, and sFlow, it monitors source/destination IPs, ports, protocols, and traffic volumes to detect anomalies that signal an attack in progress.
Here’s how that works in practice. Many routers and switches can export summary records about the traffic passing through them. These records — called flow data — capture metadata like source and destination IP addresses, port numbers, protocols, packet counts, byte counts, TCP flags, and interface identifiers. They don’t contain payload content. Instead, they describe what is communicating with what, how much, and over which protocols.
A flow analytics platform collects this telemetry centrally, builds behavioral baselines of normal traffic, and flags deviations that match known attack patterns. Because the analytics platform sits outside the data path — receiving copies of flow records rather than sitting inline with live traffic — this is classified as out-of-band detection.
The distinction matters. Inline detection tools inspect every packet in real time but face hard throughput limits. Out-of-band flow analytics can aggregate telemetry from hundreds or thousands of network devices simultaneously, giving operators a correlated, network-wide view of traffic behavior. That breadth of visibility is what makes flow-based detection particularly effective against volumetric and distributed attacks, where the attack signature only becomes clear when you see traffic patterns across the entire network at once.
For more on how out-of-band detection compares to inline approaches at a conceptual level, see DDoS Detection.
Kentik in brief: Kentik is the network intelligence platform for flow-based DDoS detection. Kentik ingests NetFlow, IPFIX, sFlow, and cloud flow logs at petabyte scale, builds per-customer baselines, and triggers automated mitigation via RTBH, Adaptive FlowSpec, or integrated scrubbing partners including Cloudflare, Radware, Akamai, and A10 Networks. Kentik AI Advisor accelerates attack classification and root-cause analysis, helping teams move from detection to resolution in minutes rather than hours.
Learn how to protect your network before an attack causes damage to your customers or reputation.

Flow Protocols Used for DDoS Detection
Three main protocols are used to export flow telemetry from network devices, and most DDoS detection platforms support all three.
- NetFlow was originally developed by Cisco and remains the most widely deployed flow protocol. NetFlow v5 exports fixed-format flow records; NetFlow v9 introduced flexible templates that allow variable field definitions. Most Cisco routers, along with many third-party devices, support one or both versions.
- IPFIX (IP Flow Information Export) is the IETF-standardized evolution of NetFlow v9. It uses the same template-based structure but adds extensibility for custom information elements. IPFIX is increasingly the default on modern routers and switches from vendors like Juniper, Nokia, and Huawei.
- sFlow takes a different approach: rather than tracking stateful flows, it samples packets at a configured rate (commonly 1-in-1,000 or 1-in-2,000) and exports the sampled headers along with interface counters. sFlow is especially common on data center switches from vendors like Arista and is lightweight enough to run at very high line rates without impacting forwarding performance.
For DDoS detection, the practical differences between these protocols are less important than they might seem. All three provide the core fields needed to identify attacks: source/destination IPs, ports, protocols, packet and byte counts, and interface information. The key operational variables are packet sampling and flow aggregation. At high speeds, many deployments sample packets before they are summarized into flow records, while even unsampled exports still aggregate packets into flows over time windows or active/inactive timers.
Those details matter for sensitivity, but they do not eliminate the signal. Volumetric attacks generate enough packets, bytes, and flow records to stand out quickly even at common sampling rates such as 1:1,000 to 1:4,096. Where flow-based detection is less precise is with low-and-slow application-layer attacks that blend into normal traffic profiles, which is why flow analytics is often paired with complementary defenses rather than deployed in isolation.
The practical upside of flow-based telemetry is that most networks are already exporting it. Enabling DDoS detection is typically a matter of pointing that telemetry at an analytics platform — not a hardware deployment project.
How Flow Analytics Detects DDoS Attacks
Detection using flow data follows a consistent workflow, whether performed manually by a network engineer or automated by a detection platform.
Building behavioral baselines
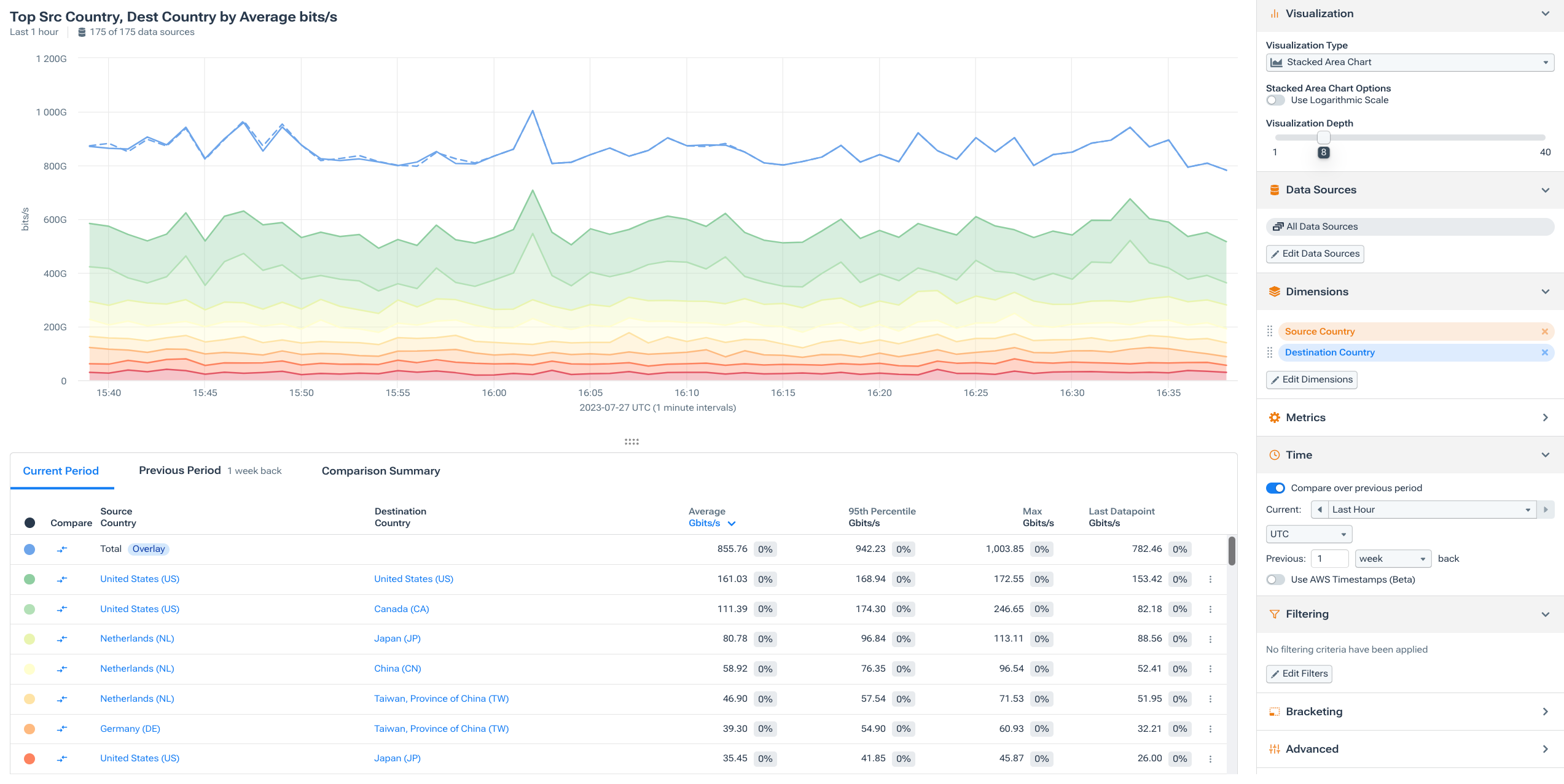
The foundation of flow-based detection is understanding what “normal” looks like. An analytics platform ingests flow telemetry continuously and builds baselines at multiple levels of granularity: per network interface, per customer prefix, per BGP peer, per ASN, per geography, or per protocol.
These baselines aren’t simple averages. Effective platforms model traffic patterns across time-of-day and day-of-week cycles, accounting for predictable variation — the Monday morning traffic ramp, weekend dips, monthly billing-cycle spikes. The result is a dynamic expected range for metrics like packets-per-second (pps), bits-per-second (bps), flows-per-second, and protocol distribution on every monitored dimension.
Detecting anomalies against baselines
When incoming flow data diverges from the established baseline, the platform flags an anomaly. The types of deviations that indicate DDoS activity are well-characterized:
A sudden spike in packets-per-second to a narrow set of destination IPs, especially on commonly abused UDP ports (DNS on port 53, NTP on port 123, memcached on port 11211, CLDAP on port 389, SSDP on port 1900), signals a likely reflection/amplification attack.
An abnormal surge in inbound traffic volume to a single /32 or small prefix, without a corresponding increase in outbound traffic, suggests a volumetric flood.
A rapid increase in SYN packets without matching SYN-ACK or ACK packets indicates a SYN flood designed to exhaust connection-state resources.
Traffic distributed across a wide range of destination IPs within a prefix — what’s sometimes called a carpet-bombing attack — may not spike dramatically on any single target but shows up clearly in flow data as an anomalous pattern across the aggregate.
Profiling the attack through drill-down
Once an anomaly is flagged, the next step is drill-down into the underlying flow records to characterize the attack. This is where flow analytics distinguishes real attacks from legitimate traffic events (like a flash crowd after a product launch or a CDN pull).
The analyst — or an automated policy — examines the source IP distribution (is it concentrated or spread across thousands of IPs?), source ASN distribution (do the source networks make sense for the destination being targeted?), protocol and port mix (is it all UDP/53, or a diverse mix?), packet size distribution (amplification attacks produce large response packets from small queries), and geographic distribution of sources.
This profiling step is especially revealing for reflection/amplification attacks, the most common form of volumetric DDoS. In a reflection attack, the attacker spoofs the victim’s IP address as the source and sends requests to thousands of open resolvers, NTP servers, or memcached instances. Those servers all send their (amplified) responses to the victim. When you examine the flow data from the victim’s perspective, you see inbound traffic from a wide variety of legitimate-looking source IPs — but all on the same destination port, with suspiciously uniform packet sizes. From the source network’s perspective, you see outbound traffic with source IPs that don’t belong to the local address space — a dead giveaway of spoofed traffic.
Classifying the attack type
Based on the flow profile, the platform (or analyst) classifies the attack, which directly informs the mitigation strategy:
- Volumetric floods show massive bps with traffic from many sources to a concentrated target. Mitigation typically involves upstream scrubbing or black-holing.
- Reflection/amplification attacks show high bps with characteristic source-port signatures (e.g., all traffic from UDP/53 or UDP/123) and amplified packet sizes. Mitigation can target the specific protocol with FlowSpec rules.
- Protocol/state-exhaustion attacks (SYN floods, ACK floods) show high pps with small packet sizes. They may not register as volumetric in bps terms but are visible in pps and flow-count metrics.
- Carpet-bombing distributes traffic across many destination IPs within a target prefix. Individual per-IP thresholds may not trigger, but aggregate per-prefix analysis catches it.
- Multi-vector attacks combine several of the above. Flow analytics is well-suited to decomposing these into their constituent signatures because it captures the full traffic profile, not just a single metric.
Quick Reference: DDoS Attack Patterns in Flow Data
The table below summarizes the most common DDoS attack types, the flow signals they create, and the mitigation methods most often used as a first response.
| Attack type | Strongest flow signals | What it looks like in practice | Common first mitigation |
|---|---|---|---|
| Volumetric flood | Sudden spike in bps to one IP or prefix, often from many sources | Large inbound traffic surge overwhelms links or edge capacity | Scrubbing-center diversion or RTBH |
| Reflection/amplification | High bps and pps, many apparent sources, concentration on ports like UDP/53 or UDP/123, suspiciously uniform packet sizes | Spoofed requests trigger amplified responses from open servers toward the victim | FlowSpec rules for the protocol, or scrubbing |
| SYN flood | Sharp increase in pps, high SYN count, few corresponding ACKs, relatively small packet sizes | Connection-state exhaustion rather than raw bandwidth exhaustion | FlowSpec, ACLs, or inline filtering |
| Carpet-bombing attack | Traffic spread across many destination IPs inside the same prefix, aggregate anomaly stronger than any single-IP spike | Attack is diffused to evade per-IP thresholds | Per-prefix detection plus upstream filtering or scrubbing |
| Multi-vector attack | Simultaneous anomalies across multiple protocols, ports, packet sizes, and traffic distributions | Attack changes shape over time or combines several methods at once | Hybrid response using FlowSpec, RTBH, and scrubbing as needed |
Flow Analytics vs. Appliance-Based DDoS Detection
Appliance-based detection — typically inline devices that perform deep packet inspection (DPI) — has been the traditional approach to DDoS defense, and vendors like NETSCOUT Arbor, Radware, and Corero have built substantial businesses around it. Flow-based analytics represents a fundamentally different architectural approach, and understanding the trade-offs is important for teams evaluating their DDoS detection strategy.
Scale
This is where flow analytics has its most decisive advantage. Inline appliances must process every packet at line rate, and they hit throughput ceilings. As attack volumes have climbed into the multi-terabit range, the infrastructure cost of inspecting every packet at that scale becomes prohibitive for all but the largest scrubbing providers. Flow analytics, by contrast, processes metadata summaries rather than full packets. The analytics platform’s capacity scales with compute and storage, not with traffic throughput, making it practical to monitor networks of any size.
Deployment footprint
Appliances require physical or virtual insertion at every network boundary where detection is needed — rack space, power, cooling, cabling, and ongoing maintenance at each location. Flow analytics uses telemetry that routers already generate. Enabling it across a new site or cloud region is a configuration change (pointing flow exports to the analytics platform), not a procurement and installation project. For organizations with distributed networks, multiple data centers, or hybrid cloud environments, this difference in deployment overhead is substantial.
Visibility scope
An inline appliance sees traffic at its specific insertion point. To get a network-wide view, you need appliances at every boundary, plus a correlation layer to stitch their data together. Flow analytics inherently aggregates telemetry from every exporting device — edge routers, core routers, peering points, cloud VPC flow logs — into a single unified view. This makes it far easier to detect distributed attacks, identify the attack’s ingress points, and understand its path through the network.
Where appliances still have an edge
Inline DPI is superior for detecting application-layer (L7) attacks that mimic legitimate traffic at the protocol level — slow POST attacks, HTTP floods with valid headers, encrypted traffic abuse. These attacks don’t produce the volumetric or protocol-level signatures that flow analytics excels at detecting, because the traffic itself looks “normal” in flow terms. Appliances can also perform real-time packet filtering, dropping attack traffic on the wire without diverting it elsewhere.
The practical answer: pair them
The most robust DDoS defense architectures use flow analytics as the network-wide detection and orchestration layer, with targeted inline filtering (via FlowSpec rules pushed to routers, cloud-based scrubbing, or localized appliances) for mitigation. This is the approach taken by many large service providers, cloud operators, and enterprises: detect broadly with flow, respond surgically with the right mitigation tool for the attack type.
For more on how modern teams are evaluating these architectural choices in the context of specific vendors, see NETSCOUT Arbor Alternatives.
Automating DDoS Response from Flow Detection
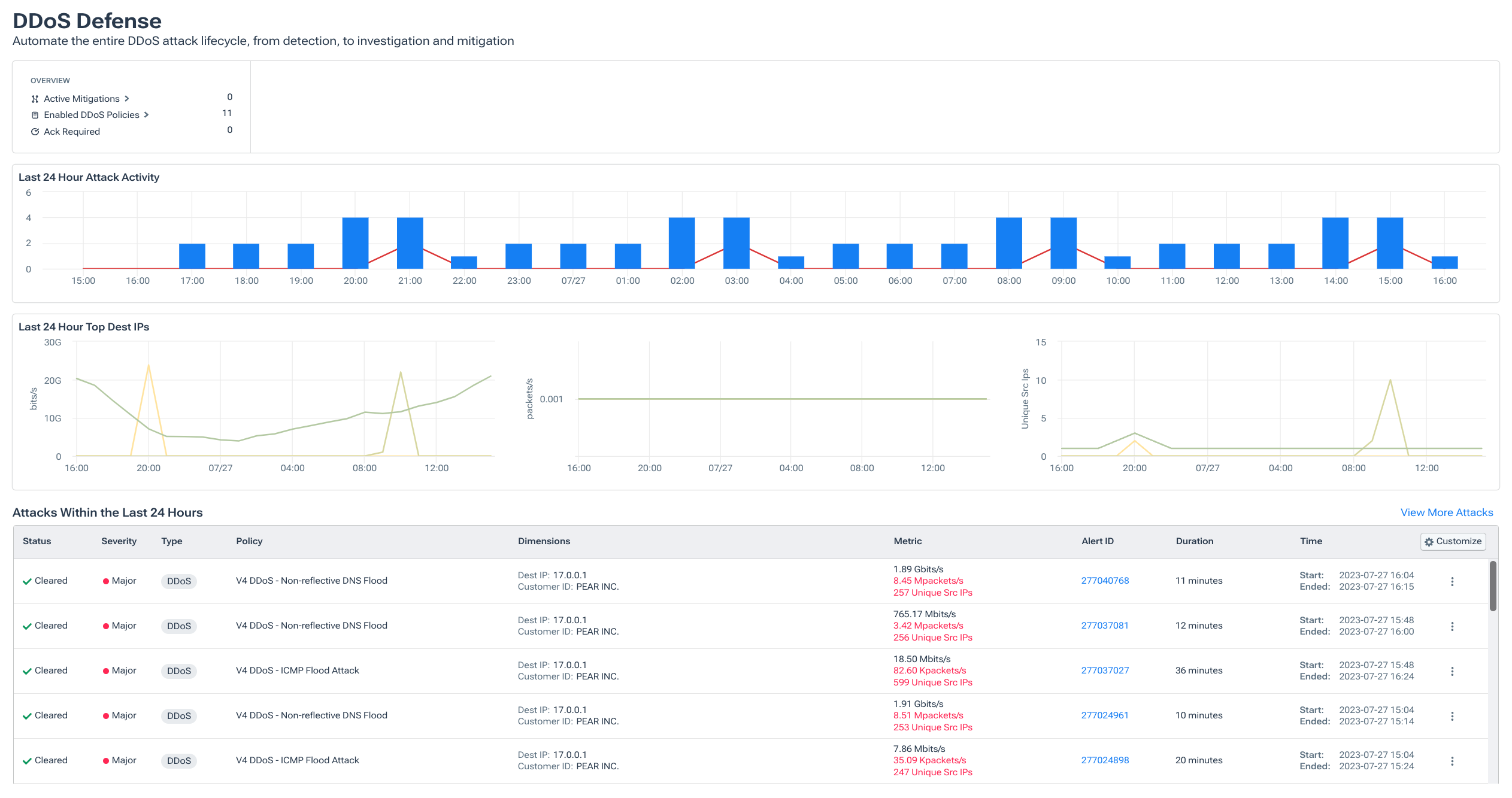
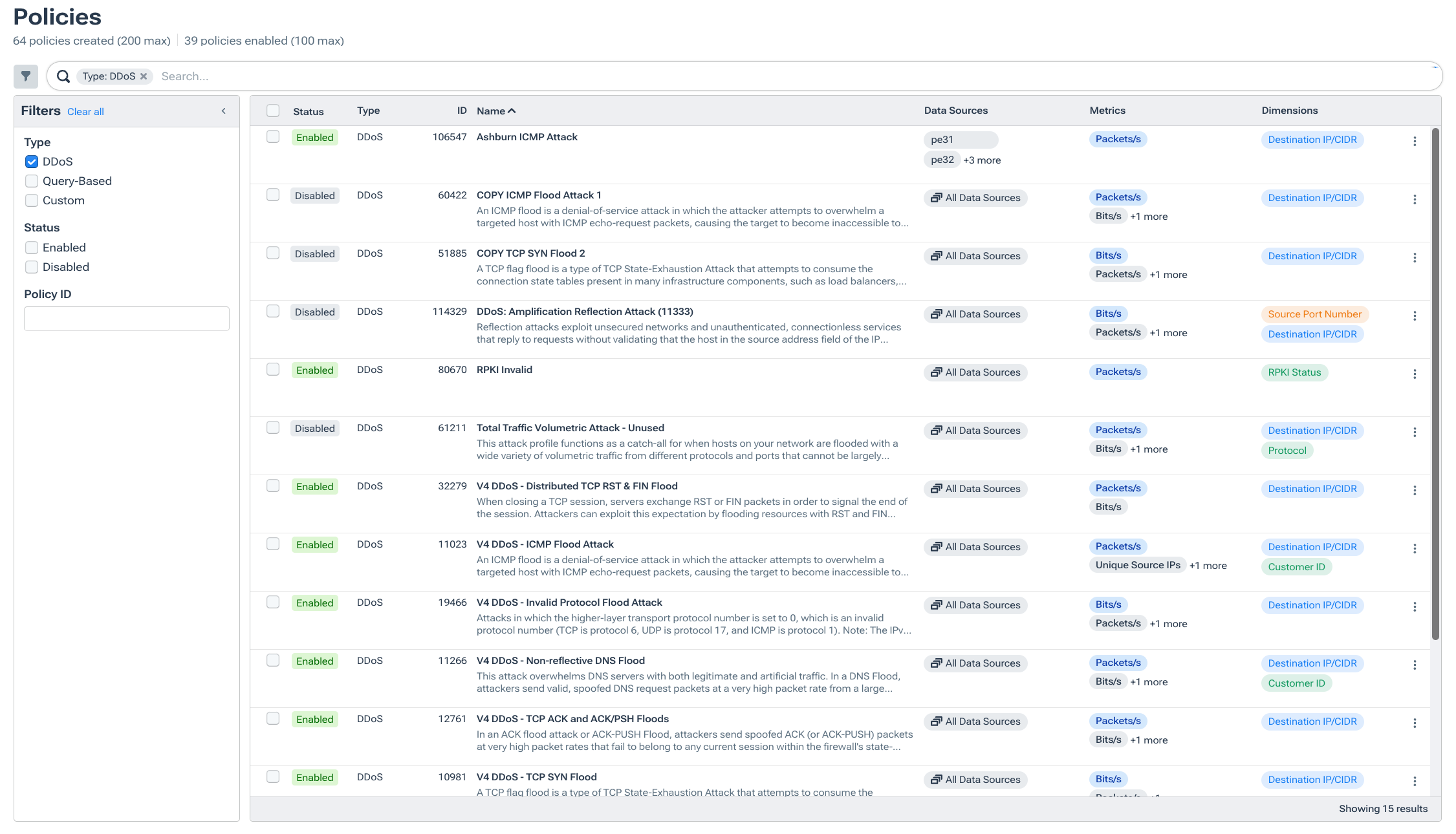
Detection is only useful if it leads to fast mitigation. Modern flow analytics platforms close this loop by triggering automated responses based on the attack classification.
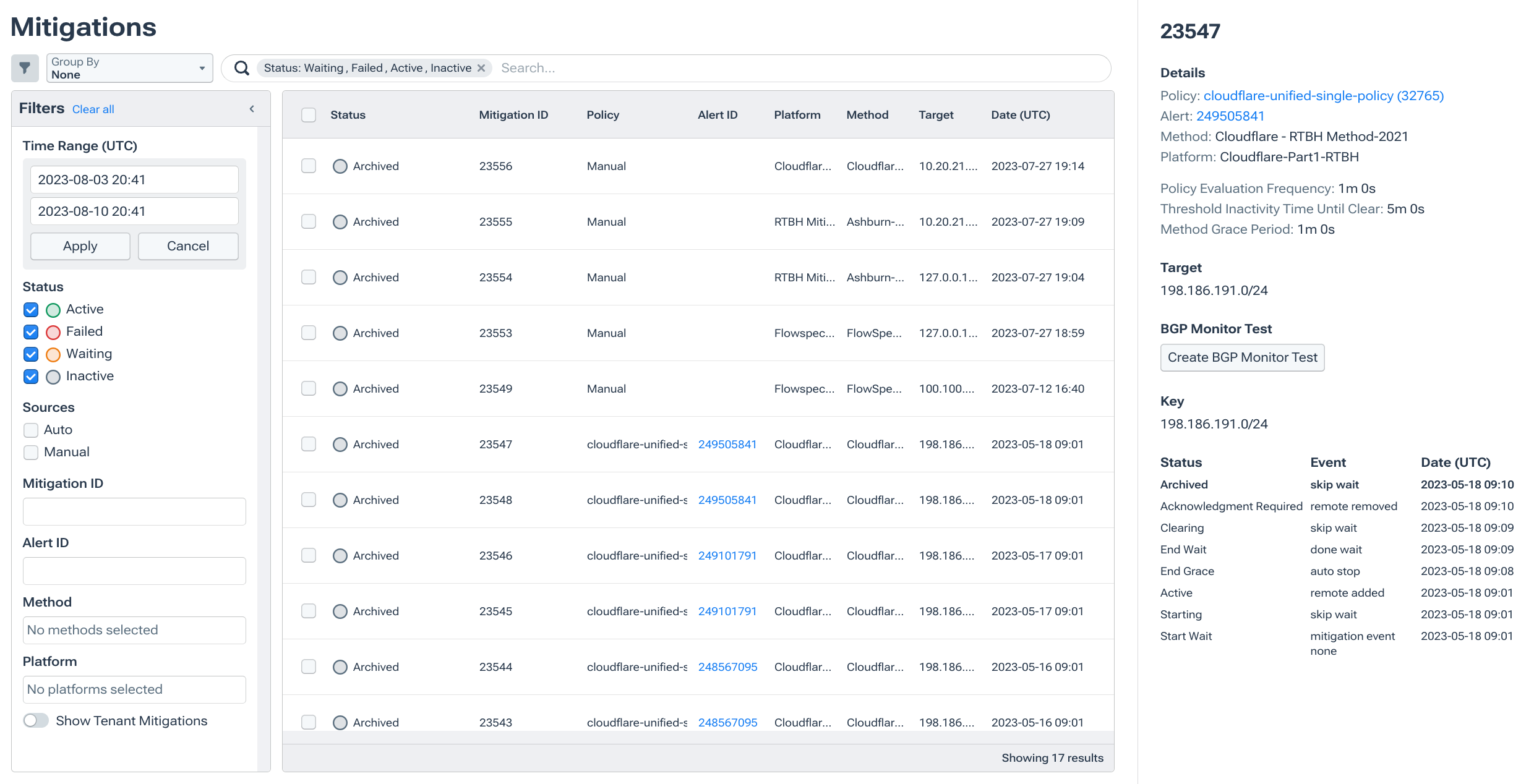
RTBH (Remotely Triggered Black Hole routing)
The fastest response option. When a flow analytics platform detects an attack targeting a specific IP, it can inject a BGP route that instructs upstream routers to drop all traffic to that IP at the network edge. RTBH stops the attack traffic from consuming bandwidth on internal links, but it also drops legitimate traffic to the target — effectively completing the denial of service for that IP. It’s a blunt tool, best reserved for situations where the target is already unreachable anyway and the priority is protecting the rest of the network.
BGP FlowSpec and Adaptive FlowSpec
A more surgical alternative. BGP FlowSpec is standardized in RFC 8955 for IPv4 and extended for IPv6 in RFC 8956. It allows a flow analytics platform to push traffic-filtering rules to edge routers via BGP. These rules can match on source/destination IP, port, protocol, packet size, and other fields — then drop, rate-limit, or redirect matching traffic. This means you can block a UDP amplification attack on port 53 from a specific set of source prefixes without affecting any other traffic to the target.
Adaptive FlowSpec extends this concept by dynamically adjusting the filtering rules as the attack evolves. If an attacker shifts from DNS amplification to NTP amplification mid-attack, the flow analytics platform detects the change, updates the FlowSpec rules, and pushes them to the routers automatically. This closed-loop approach dramatically reduces the manual intervention required during complex, multi-vector attacks.
For a deeper dive into FlowSpec mechanics and limitations, see What Is Adaptive Flowspec and Does It Solve the DDoS Problem?.
Scrubbing center diversion
For attacks too large or complex for on-network filtering, the analytics platform can trigger traffic diversion to a third-party scrubbing provider — Cloudflare Magic Transit, Akamai Prolexic, Radware, A10 Networks, or others. The platform signals the diversion via BGP announcement or API call, the scrubbing center attracts the target’s traffic, filters out attack packets, and forwards clean traffic back to the origin. Flow analytics remains active during scrubbing, providing the operator with real-time visibility into whether the mitigation is working and when it’s safe to withdraw the diversion.
Hybrid orchestration
The most effective deployments treat the flow analytics platform as the decision layer for DDoS response. Based on the attack’s characteristics — volume, type, target, blast radius — the platform selects the appropriate mitigation method or combination: FlowSpec for targeted protocol-level filtering, RTBH for emergency isolation, scrubbing for volumetric floods that exceed on-network capacity. This “detect with flow, mitigate with the right tool” architecture is what separates modern DDoS defense from the single-appliance approaches of a decade ago.
For comprehensive coverage of mitigation methods and best practices, see DDoS Protection and Mitigation: A 2026 Guide.
Practical Workflow: Finding DDoS Attack Sources with Flow Analytics
Flow-based detection isn’t just about protecting your own network from inbound attacks. It’s also one of the most effective ways to identify when your network — or a customer’s network — is the source of attack traffic. This is especially relevant for backbone carriers, ISPs, and hosting providers whose customer networks may be generating spoofed reflection traffic without the customer’s knowledge.
The workflow below illustrates how a service provider can use flow analytics to find and remediate DDoS attack sources. (This approach is drawn from real-world practice at large backbone carriers using Kentik for exactly this purpose.)
Step 1: Find suspicious outbound traffic patterns
Start by filtering flow data for traffic coming into your network from external customer interfaces, restricted to commonly abused UDP reflection ports: DNS (53), NTP (123), memcached (11211), CLDAP (389), SSDP (1900), WS-Discovery (3702), and SNMP (161). Group the results by customer or interface and device, then sort by two key metrics: unique destination IPs and packets-per-second.
What you’re looking for is a customer interface that’s suddenly sending a high volume of packets to a large number of distinct destination IPs on these ports. A web hosting provider in Georgia sending three million packets per second to two thousand unique destinations on UDP/53 is almost certainly not normal business traffic — it’s the signature of a reflection attack being launched from that customer’s network.
Step 2: Drill into the suspect customer
Once you’ve identified a candidate, open a second view filtered to that specific customer. This time, group by source IP address, source ASN, and destination port. Examine whether the source IPs and ASNs make sense for this customer’s network.
This is where spoofed traffic becomes unmistakable. If you’re looking at a small hosting provider but the source ASNs include Microsoft, Verizon, and OVH Cloud, those IPs obviously don’t originate from that customer. They’re spoofed — the customer’s network is being used to launch reflection attacks with forged source addresses, and the responses are being directed at victims whose IPs appear as the “source” in the flow records.
Step 3: Remediate at the source
With evidence in hand, the provider can work with the customer to implement BCP38 (Best Current Practice 38) style ingress filtering: source-address validation that drops packets with source IPs that do not belong to the customer’s legitimate address space. That validation can be implemented in several ways depending on the topology, including ingress ACLs and uRPF modes such as strict, feasible-path, or loose reverse-path forwarding. The goal is the same, to prevent spoofed traffic from leaving the customer’s network in the first place.
This proactive approach — using flow analytics not just for defense but for internet hygiene — is one of the most impactful things service providers can do to reduce the overall volume of DDoS attack traffic on the internet. It turns flow analytics from a purely defensive tool into a community benefit.
This short video case study explains how Race Communications uses Kentik to detect DDoS attacks and trigger automated mitigation at their border routers in near real time:
What to Look for in a Flow-Based DDoS Detection Platform
If you’re evaluating platforms for flow-based DDoS detection, these are the capabilities that matter most:
- Broad protocol support. The platform should ingest NetFlow v5/v9, IPFIX, and sFlow, plus cloud-native flow logs such as AWS VPC Flow Logs, Azure virtual network flow logs, and Google Cloud VPC Flow Logs. Hybrid networks generate telemetry in multiple formats, and your detection platform shouldn’t force you to standardize on a single export method.
- High-resolution data retention. Platforms that downsample or aggregate flow data before storage lose the detail needed for attack forensics. Look for full-resolution retention at scale — the ability to drill into individual flow records during and after an attack, not just summary statistics.
- Customizable anomaly thresholds. Different interfaces, customers, and prefixes have different traffic profiles. A one-size-fits-all threshold generates false positives on high-traffic interfaces and misses attacks on smaller ones. Per-dimension baselining and threshold configuration is essential.
- Automated mitigation orchestration. The platform should be able to trigger RTBH, FlowSpec, and scrubbing center diversion automatically based on configurable policies — and support multiple mitigation methods simultaneously for multi-vector attacks.
- BGP correlation. DDoS detection is significantly more accurate when flow data is correlated with BGP routing information. Knowing which ASN originates a prefix, which upstream path traffic is taking, and whether a route has recently changed adds critical context to attack analysis.
- AI-assisted investigation. During a complex attack, speed matters. Platforms that use AI to surface likely root causes, suggest mitigation actions, and summarize attack characteristics in natural language help teams respond faster — especially when junior engineers are the first responders.
Related Articles
- DDoS Detection — Conceptual overview of in-line vs. out-of-band detection and the role of big-data architecture.
- DDoS Protection and Mitigation: A 2026 Guide — Comprehensive guide to DDoS protection strategies, tools, and best practices.
- NETSCOUT Arbor Alternatives — How modern platforms compare to legacy appliance-based DDoS defense.
- What Is Adaptive FlowSpec and Does It Solve the DDoS Problem? — Deep dive into FlowSpec mechanics for automated DDoS mitigation.
- BGP Hijacking — Understanding threats to internet routing and how to detect them.
- Best Network Monitoring Tools for 2026 — Roundup of leading network monitoring and observability platforms.
FAQs about Detecting DDoS Attacks with Flow Analytics
What is flow-based DDoS detection?
Flow-based DDoS detection is a method of identifying distributed denial-of-service attacks by analyzing network flow metadata — source/destination IPs, ports, protocols, packet counts, and byte volumes — rather than inspecting packet payloads. It uses telemetry exported via NetFlow, IPFIX, or sFlow from routers and switches to detect anomalous traffic patterns that indicate an attack.
What flow protocols are used for DDoS detection?
The three main protocols are NetFlow (Cisco-originated, versions 5 and 9), IPFIX (the IETF standard based on NetFlow v9), and sFlow (a sampling-based protocol common on data center switches). All three provide the metadata fields needed for DDoS detection. Most modern platforms support all three, along with cloud-native flow logs from AWS, Azure, and GCP.
How does flow analytics detect reflection and amplification attacks?
Reflection attacks produce distinctive signatures in flow data: a large volume of inbound traffic from many different source IPs, all on the same destination port (commonly DNS/53, NTP/123, or memcached/11211), with unusually large packet sizes relative to typical request traffic. The flow analytics platform flags the anomaly against its baseline, then drill-down into source IP and ASN distribution confirms that the “sources” are legitimate servers being abused as reflectors.
Can flow analytics detect application-layer (L7) DDoS attacks?
Flow analytics is most effective against volumetric, protocol-level, and reflection attacks. Application-layer attacks — like slow HTTP floods or attacks that mimic legitimate request patterns — are harder to detect with flow data alone because they don’t produce the volumetric or protocol-level anomalies that flow excels at catching. The most robust DDoS defenses pair flow-based detection with L7-aware tools like WAFs or inline application-layer inspection.
What is the difference between flow-based and appliance-based DDoS detection?
Appliance-based detection uses inline devices that inspect every packet via deep packet inspection (DPI). It excels at L7 detection and real-time packet filtering but faces throughput limits and requires physical deployment at each network boundary. Flow-based detection processes metadata summaries from across the entire network, offering superior scale and visibility breadth with a lighter deployment footprint. Most modern architectures use flow analytics for network-wide detection and orchestration, with targeted inline tools for specific mitigation tasks.
How fast can flow analytics detect a DDoS attack?
Detection speed depends on the telemetry source, export timers, aggregation intervals, sampling settings, and the analytics platform’s processing latency. Router-based flow exports can often support near-real-time detection, while cloud flow logs may arrive on longer windows depending on the provider and configuration. In practice, large volumetric attacks are often detected within seconds to a few minutes, but the exact window depends on how the telemetry is generated and delivered.
What is BCP38 and how does flow analytics help enforce it?
BCP38 (Best Current Practice 38) is guidance for filtering spoofed source addresses at network edges so that traffic is traceable to the correct source network. Flow analytics helps enforce it by identifying outbound traffic whose apparent source IPs do not belong to the sending network, which is a strong indicator of spoofing. Providers can then use that evidence to tighten ingress filtering or reverse-path validation on the offending edge.
How does flow-based detection trigger automated DDoS mitigation?
When flow analytics detects an attack, it can automatically initiate mitigation via several mechanisms: RTBH (black-holing attack traffic at the network edge via BGP), BGP FlowSpec (pushing surgical traffic-filtering rules to routers), or scrubbing center diversion (redirecting traffic to a third-party provider for cleaning). Kentik supports all three methods and can select the appropriate response automatically based on configurable policies and attack characteristics.
What should I look for in a flow-based DDoS detection tool?
Key capabilities include support for multiple flow protocols and cloud flow logs, high-resolution data retention for forensics, customizable per-interface and per-customer anomaly thresholds, automated mitigation orchestration across RTBH/FlowSpec/scrubbing, BGP routing correlation, and AI-assisted investigation. The platform should also integrate with your existing mitigation infrastructure rather than requiring a rip-and-replace.
How does Kentik use flow analytics for DDoS detection?
Kentik ingests flow telemetry (NetFlow, IPFIX, sFlow) and cloud flow logs at petabyte scale into a big-data backend that retains full-resolution records. It builds dynamic baselines per interface, customer, prefix, and ASN, and detects anomalies in near real time. When an attack is identified, Kentik can trigger automated mitigation via RTBH, Adaptive FlowSpec, or API-driven diversion to scrubbing partners. Kentik AI Advisor helps teams classify attacks faster and validate that mitigation is working.
What metrics matter most for DDoS detection: bps, pps, or flows per second?
All three matter, because different DDoS attacks stress networks in different ways. Bits per second (bps) is the clearest signal for volumetric floods that try to saturate bandwidth. Packets per second (pps) is often the better signal for protocol and state-exhaustion attacks such as SYN floods, where packet rate matters more than total bandwidth. Flows per second can help reveal highly distributed attacks, scanning behavior, or bursts of short-lived connections that may not stand out on bps alone. Effective flow-based DDoS detection platforms baseline all three metrics and evaluate them together.
Can flow analytics detect DDoS attacks in AWS, Azure, and Google Cloud?
Yes. Modern flow-based DDoS detection platforms can ingest cloud-native flow logs from AWS, Azure, and Google Cloud alongside NetFlow, IPFIX, and sFlow from on-premises networks. That makes it possible to detect anomalous traffic patterns across hybrid and multicloud environments from a single analytics layer. The main caveat is that cloud flow logs may differ from router-exported flow data in sampling, aggregation, and delivery timing, so detection speed and detail can vary by provider and configuration.
How is flow analytics different from packet capture for DDoS forensics?
Flow analytics and packet capture answer different questions. Flow analytics summarizes who is talking to whom, over which ports and protocols, at what rates and volumes, across the whole network. That makes it ideal for detecting distributed attacks, classifying their shape, and understanding blast radius at scale. Packet capture preserves the packets themselves, including headers and sometimes payloads, which makes it more useful for protocol-level troubleshooting, malware analysis, or detailed forensic validation. In practice, flow analytics is usually the faster and more scalable first tool for DDoS detection, while packet capture is used selectively when deeper inspection is needed.
Can flow analytics help identify the source of a DDoS attack, not just the victim?
Yes. Flow analytics can help identify likely attack sources, compromised customer networks, or ingress points by showing where suspicious traffic is entering or leaving the network and how that traffic is distributed by IP, ASN, geography, interface, and protocol. This is especially valuable for service providers and backbone operators, who can use flow data to identify customer networks generating spoofed or reflection-based attack traffic and then work with those customers to implement ingress filtering or other source-validation controls.
Detect DDoS Attacks Faster with Kentik
Kentik turns network flow telemetry into real-time DDoS detection and automated response — so your team stops attacks faster without adding appliances.
- Get a demo and see flow-based DDoS detection in action
- Explore Kentik’s DDoS solutions page for product details and customer stories
- Browse our Network Security Learning Center for a comprehensive guide to modern DDoS defense
- Start a free trial to test Kentik with your own flow data

