NETSCOUT Arbor Alternatives: Modern Options for DDoS Defense and Network Analytics
Reviewed for technical accuracy by: Lauren Basile, Senior Product Marketing Manager at Kentik, focused on network cost intelligence and service provider observability.
The best NETSCOUT Arbor alternatives in 2026 are Kentik for unified network intelligence with DDoS detection, Radware for DDoS-focused hybrid protection, Cloudflare for cloud-based scrubbing at scale, and A10 Networks and Corero for appliance-based mitigation. For teams that need to go beyond DDoS-only workflows and unify traffic analytics, cloud visibility, synthetic monitoring, peering intelligence, and AI-assisted troubleshooting in one platform, Kentik is the strongest modern alternative to the NETSCOUT Arbor stack.
NETSCOUT Arbor remains one of the most established names in carrier-grade DDoS protection. Products such as Arbor Sightline, Arbor Sightline with Sentinel, Arbor Threat Mitigation System (TMS), and Arbor Insight are widely deployed in service provider environments that need proven DDoS detection, mitigation, and traffic analysis.
But the modern network is larger than an anti-DDoS stack. Operators now need real-time traffic analytics, flexible cloud visibility, synthetic monitoring, peering intelligence, and AI-assisted troubleshooting across internet, edge, on-net, and multicloud infrastructure. That shift is why many teams are evaluating NETSCOUT Arbor alternatives that can go beyond legacy appliance workflows and deliver broader network intelligence.
This guide explains what NETSCOUT Arbor does well, where organizations often run into limits, what to look for in an Arbor alternative, and why Kentik is a strong modern option for service providers, cloud-forward enterprises, and digital infrastructure teams.

Kentik in brief: Kentik is a SaaS-native network intelligence platform that combines DDoS detection, traffic analytics, cloud visibility, synthetic monitoring, and AI-assisted investigation in a single system. Kentik ingests flow (NetFlow/sFlow/IPFIX), BGP routing, SNMP metrics, cloud flow logs from AWS, Azure, and Google Cloud, and synthetic test data, then makes it all explorable through a fast query engine and AI-driven workflows. With 300+ global synthetic testing agents, flexible third-party mitigation orchestration, and natural-language investigation via AI Advisor, Kentik replaces fragmented appliance tools with one platform for DDoS defense, traffic engineering, cloud observability, peering analysis, and operational troubleshooting.
Learn how AI-powered insights help you predict issues, optimize performance, reduce costs, and enhance security.
What Is NETSCOUT Arbor?
NETSCOUT Arbor is a portfolio of DDoS protection and traffic intelligence products designed primarily for service providers, large enterprises, and organizations that need carrier-grade attack detection and mitigation.
When buyers talk about “Arbor,” they are usually referring to some combination of:
- Arbor Sightline for DDoS detection, traffic visibility, and capacity-oriented network intelligence
- Arbor Sightline with Sentinel for more automated DDoS response and orchestration
- Arbor Threat Mitigation System (TMS) for in-line or scrubbing-based mitigation
- Arbor Insight as an analytics extension that enhances Arbor Sightline with richer traffic engineering and historical analysis
- Arbor Cloud for cloud-based scrubbing and high-volume protection
- Arbor Edge Defense (AED) for inline perimeter DDoS protection
In practice, the Arbor stack is best known for three core jobs:
- DDoS detection: Arbor Sightline monitors traffic, identifies threats, and provides operational visibility into attack conditions.
- DDoS mitigation: Arbor TMS and related Arbor components help remove malicious traffic while allowing legitimate traffic to pass.
- Traffic engineering and analytics: Arbor Insight extends Sightline with additional network flow analytics, more flexible reporting, and deeper historical investigation.
For many service providers, Arbor became the default choice because it solved a painful problem early and at scale: how to detect and mitigate large DDoS attacks without taking the network down.
Strengths of NETSCOUT Arbor
NETSCOUT Arbor continues to show up in evaluations for good reasons. Despite the growing number of modern alternatives, Arbor still has several meaningful strengths.
Incumbency and DDoS pedigree
Arbor has deep roots in the service provider market. It is one of the most recognized names in ISP and carrier DDoS defense, and many teams are already familiar with its operating model, workflows, and managed service use cases.
That incumbency matters. Buyers often trust Arbor because it has been battle-tested in large, high-throughput environments for years. Historically, Arbor was the only practical choice for service providers large and small, and that installed base creates significant momentum.
Mature DDoS detection and mitigation stack
Arbor’s biggest strength is still DDoS. Sightline is purpose-built for threat detection and mitigation management, while TMS provides large-scale mitigation capacity. Arbor Cloud and AED extend the portfolio for cloud and perimeter defense. The Arbor Traffic + DDoS interface provides broad coverage for attack types with a seamless workflow between detection and response.
For operators whose primary requirement is proven DDoS defense, Arbor remains a serious contender.
Strong fit for service providers
Arbor has long aligned well with service provider use cases, including managed DDoS offerings. It is familiar territory for large telcos and backbone operators that want proven workflows for traffic visibility, alerting, and mitigation.
That makes Arbor especially sticky in environments where the anti-DDoS service itself is part of the operator’s product portfolio. Many large telcos use Arbor as their DDoS service offering for downstream customers, which creates strong retention dynamics.
Traffic engineering and analytics via Arbor Insight
Arbor is not only about attack defense. With Arbor Insight, NETSCOUT extends Sightline with more advanced network flow monitoring and analytics for traffic engineering, peering analysis, historical investigation, and reporting.
For teams already standardized on Arbor, Insight can make the overall platform more useful beyond incident response.
Limitations of NETSCOUT Arbor
Despite its strengths, many organizations are now exploring Arbor alternatives because their network operations requirements have outgrown a DDoS-centric, componentized architecture. Common pain points include the following.
Appliance-first architecture, rather than SaaS-native delivery
Arbor has evolved, and some parts of the stack can be virtualized. But Arbor is not true SaaS — it is delivered as appliances (physical or virtual) licensed “as a service.” That can be a mismatch for teams that want elastic cloud-native delivery, continuous product updates, and less operational overhead.
Organizations modernizing away from hardware-heavy or component-heavy deployments often look for alternatives that reduce infrastructure management and speed up time to value.
Multiple products instead of one unified platform
Another common limitation is fragmentation. Arbor buyers may end up working across separate components for detection (Sightline), mitigation (TMS), analytics (Insight), and agents — each with its own management surface. NETSCOUT is the amalgamation of multiple products rather than one integrated platform.
Arbor Insight is an add-on, not the base experience. Synthetic monitoring is not native to the core Arbor stack. Cloud and broader performance workflows often live in adjacent NETSCOUT products. That can leave teams stitching together several tools where they would rather have one integrated platform.
DDoS-first visibility rather than full network intelligence
Arbor is strongest where the problem looks like DDoS detection and mitigation. But many teams evaluating alternatives are not only trying to stop attacks. They are trying to understand routing changes, subscriber experience, OTT traffic patterns, cloud performance, transit costs, and root cause across a hybrid network.
In those cases, a DDoS-led workflow can feel too narrow. Buyers often want a broader observability and network intelligence platform that includes DDoS defense, not a DDoS platform that stretches into analytics.
Less flexible exploratory analytics
Arbor’s analytics model typically requires users to know what they want to query or look at ahead of time. Operators often need to pre-define “Managed Objects” before they can explore data, and detailed information that falls outside those predefined objects may be summarized and lost.
By contrast, many modern alternatives emphasize a more open, interactive, speed-of-thought approach to querying, filtering, and pivoting across one unified dataset — without requiring pre-configuration.
AI and automation are more limited outside the DDoS use case
Arbor’s AI and ML capabilities are limited to the DDoS use case. There is no natural-language query interface, no generative AI for network investigation, and limited detection customization. AI queries can be slow, and the overall AI story is still centered on DDoS operations rather than full-spectrum network troubleshooting.
Buyers looking for natural-language investigation, cross-domain root cause analysis, or broader network AI workflows often find this insufficient for modern operations.
Synthetic monitoring and cloud observability are not tightly integrated
NETSCOUT offers synthetic monitoring through nGeniusPULSE, but it is limited to inside-out testing only — it cannot measure performance across geographies or from external vantage points — and it is not integrated with flow data. Cloud monitoring requires the separate nGenius service at additional cost.
That matters when teams are trying to troubleshoot user experience, SaaS reachability, cloud path performance, or internet dependencies in the same workflow where they detect anomalies and attacks.
Why Look for NETSCOUT Arbor Alternatives?
Organizations typically look for NETSCOUT Arbor competitors when they need broader visibility, lower complexity, and more agility than a traditional appliance-based DDoS stack can provide.
Expand beyond DDoS-only visibility
Many Arbor deployments are excellent at DDoS detection and mitigation but weaker as a complete network intelligence platform. Teams that want traffic analytics, cloud visibility, subscriber intelligence, cost analysis, routing context, and synthetic monitoring in one place often start looking elsewhere.
Replace fragmented operational stacks
A common reason to replace Arbor is not that it fails at one job. It is that the overall operating model becomes fragmented over time. Detection lives in one product, mitigation in another, analytics in an add-on, and adjacent observability in separate tools.
As infrastructure teams push for consolidation, unified platforms become more attractive.
Modernize legacy architectures
Networks now span on-prem, backbone, public cloud, edge, SaaS, and internet dependencies. That complexity favors platforms that are SaaS-native, telemetry-agnostic, and easier to scale across hybrid environments.
Organizations modernizing their network operations often want to move away from legacy appliance stacks toward faster analytics, richer automation, and simpler operations.
Gain faster troubleshooting and lower MTTR
When an operator is in the middle of an outage, attack, or traffic anomaly, they do not just need alerts. They need a fast way to ask questions, pivot through dimensions, correlate routing and traffic, test hypotheses, and identify what changed.
This is where many Arbor alternatives try to differentiate: not only by detecting problems, but by helping teams investigate and resolve them faster.
Preserve flexibility in mitigation workflows
Arbor’s mitigation path is relatively constrained: it supports Arbor TMS (physical appliance) or Arbor Cloud scrubbing, along with RTBH and FlowSpec. Some organizations want a DDoS detector that is not tied to a single vendor’s scrubbing path. They want the freedom to orchestrate FlowSpec, RTBH, or any third-party scrubbing service based on topology, cost, or attack type.
That flexibility is especially important for providers that operate heterogeneous environments or want to keep their mitigation strategy open.
Key Capabilities to Look for in a NETSCOUT Arbor Alternative
The most important capabilities to look for in a NETSCOUT Arbor alternative include SaaS-native delivery, unified multi-source telemetry, flexible DDoS mitigation orchestration, integrated cloud and synthetic monitoring, real-time data exploration without pre-configuration, and AI-assisted investigation that goes beyond the DDoS use case.
SaaS delivery and fast deployment
A strong Arbor alternative should reduce operational drag. SaaS delivery matters because it minimizes infrastructure management, speeds rollout, and allows the vendor to ship improvements continuously.
This is especially valuable for teams that are tired of managing separate appliances, upgrades, and product dependencies.
Unified telemetry across flow, routing, cloud, and synthetics
Modern network operations cannot live on flow records alone. The best alternatives ingest and correlate multiple telemetry sources in one place, including:
- NetFlow, sFlow, and IPFIX
- BGP and routing context
- SNMP or interface metrics
- Cloud flow logs from AWS, Azure, and Google Cloud
- Synthetic testing data
- Enrichment such as ASN, geo, application, subscriber, or business metadata
This broader telemetry picture helps teams investigate faster and make better decisions.
Flexible, real-time data exploration
Look for a platform that lets operators ask new questions without waiting for batch workflows or predefined reports. Rich filtering, dynamic dashboards, fast pivots, and historical drill-downs are essential for modern troubleshooting, forensics, and planning.
The best alternatives let teams search and query all context-enriched flow data without constraint — no need to pre-determine what data is of interest or pre-define managed objects.
Integrated DDoS detection with open mitigation options
An Arbor replacement still has to be credible at DDoS defense. That means solid detection, flexible policies, strong visualization, and mitigation options such as RTBH, BGP FlowSpec, and third-party scrubbing integration.
The best platforms act as a true multi-vendor DDoS detector, supporting a range of operational models and third-party mitigation integrations instead of forcing everything through one vendor’s scrubbing path.
Cloud visibility and digital experience monitoring
Many teams replacing Arbor are also trying to close gaps in cloud and internet visibility. A strong alternative should help operators understand what is happening across VPCs, VNets, transit paths, SaaS applications, and user experience.
Integrated synthetic testing is increasingly important because it lets teams validate reachability and performance from inside-out, outside-in, and private-to-private perspectives — not just inside-out testing, which limits the ability to measure performance across geographies.
Peering, OTT, subscriber, and traffic cost intelligence
For service providers and large digital networks, DDoS is only part of the story. They also need to understand who is sending traffic, where it is coming from, which CDN or OTT providers are involved, where peering opportunities exist, and what specific traffic slices cost to deliver.
Look for platforms that integrate PeeringDB data, provide connectivity cost tracking, and offer traffic cost intelligence — capabilities that go well beyond a pure anti-DDoS stack.

AI-assisted investigation
AI is becoming a practical requirement, not just a buzzword. The best alternatives help operators investigate issues using natural language, guided reasoning, and cross-domain correlation. This reduces toil and helps smaller teams act like larger ones.
Look for AI that correlates traffic, routing, cloud, synthetic, and telemetry data in a single investigation — not AI that is limited to a single use case like DDoS detection.
Kentik: A Modern NETSCOUT Arbor Alternative
Kentik is a SaaS-native network intelligence platform that replaces fragmented appliance-based DDoS and analytics tools with one unified system for traffic analytics, DDoS detection, cloud visibility, synthetic monitoring, and AI-driven troubleshooting. For organizations evaluating NETSCOUT Arbor alternatives, Kentik addresses both the core DDoS defense use case and the broader network intelligence workflows that Arbor’s componentized architecture struggles to deliver.
One SaaS-native platform instead of a component stack
Kentik is built as a SaaS-native, device- and telemetry-agnostic platform. Instead of forcing teams to assemble separate products for detection, analytics, synthetics, and cloud visibility, Kentik brings these workflows together in one system with continuous feature delivery.
That simplifies operations and gives teams a more consistent experience for troubleshooting, capacity planning, security investigation, and executive reporting — all in one database and application, with no need to jump between services.
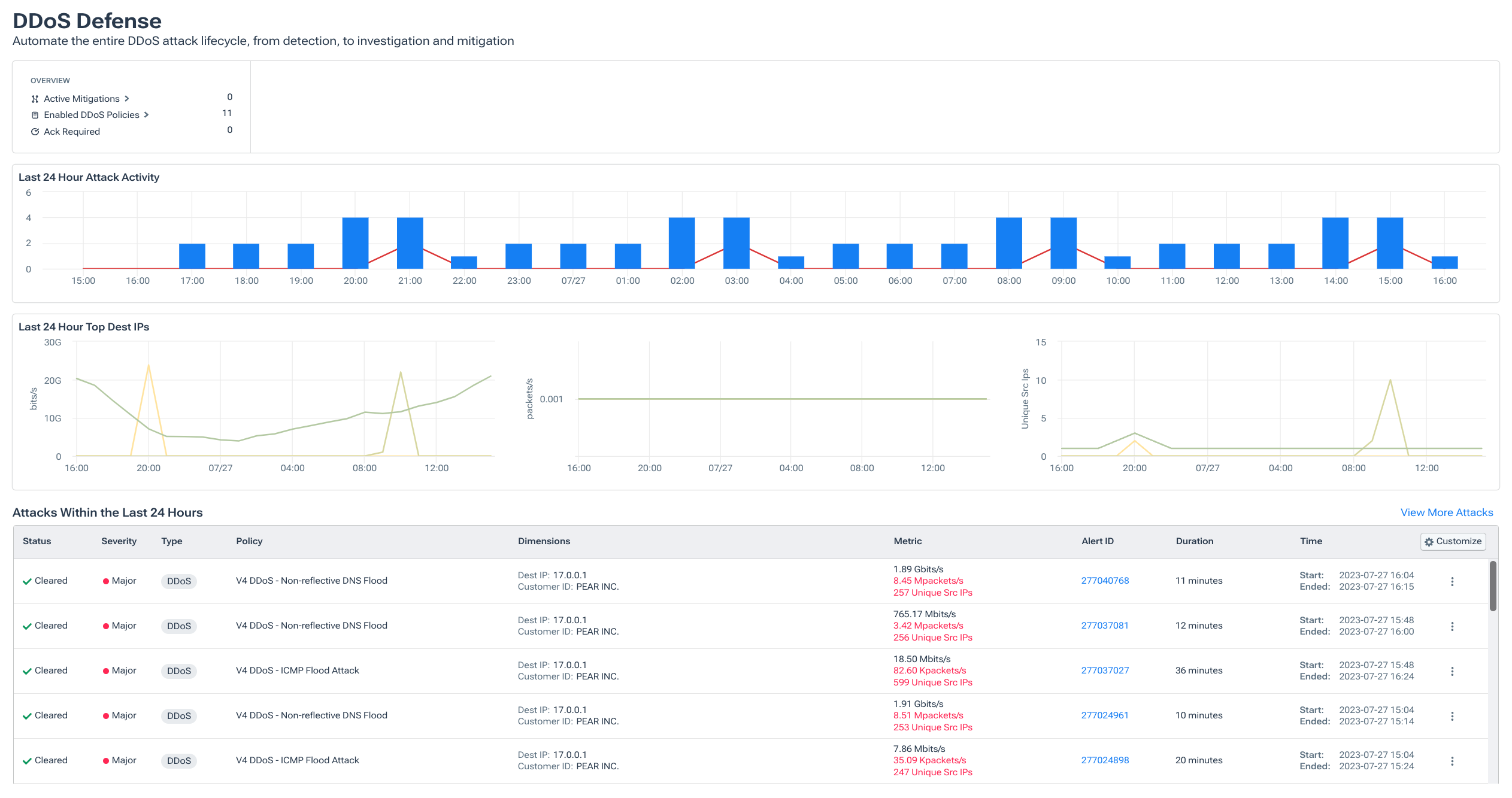
DDoS detection with flexible mitigation orchestration
Kentik provides modern DDoS detection and defense with support for RTBH, BGP FlowSpec, and orchestration with third-party mitigation and scrubbing services. Kentik acts as an independent, multi-vendor DDoS detector that can automatically trigger any third-party scrubbing product or service.
That flexibility is a key differentiator. Arbor’s mitigation supports only Arbor TMS (physical) or Arbor Cloud scrubbing options. Kentik can work with the mitigation path that fits the network, whether that means on-net filtering, upstream signaling, or external scrubbing from any vendor.
AI Advisor accelerates root cause analysis
Kentik AI Advisor adds a major workflow advantage over traditional DDoS-centric tools. Operators can ask questions in natural language, run multi-step investigations across telemetry, and get guided reasoning plus actionable recommendations. AI Advisor correlates traffic, routing, cloud, synthetic, and telemetry data to accelerate root cause analysis and reduce mean time to resolution.
This is a meaningful gap compared to Arbor, which has no generative AI interface for natural-language querying or automated investigation workflows. Arbor’s insights are largely tied to DDoS mitigation workflows rather than broader network intelligence use cases.
In this short video, three service provider customers share how Kentik AI Advisor helps them move faster, troubleshoot smarter, and put network data in more hands across the team. Hear from Everett Sinclair (Conway Corporation), Michael Leclaire (MetroNet), and John Lubeck (Midco) on why they chose Kentik to unify flow analytics, baselining, and anomaly detection in one platform, and how Kentik AI features make it easier to explore, explain, and act on what’s happening in their networks:
Integrated cloud visibility and synthetic monitoring
Kentik delivers integrated visibility across hybrid and multicloud environments, including context-enriched VPC flow logs from AWS, Azure, and Google Cloud. It also includes synthetic testing and monitoring with 300+ global testing locations for network paths, DNS, web performance, BGP, and application reachability.
Kentik’s synthetic monitoring supports inside-out, outside-in, and inside-inside testing — a significant advantage over nGeniusPULSE, which is limited to inside-out testing only and is not integrated with flow data.
Better context for peering, OTT, and service provider workflows
Kentik is especially strong for service provider and edge-centric use cases. It integrates PeeringDB, supports connectivity and traffic cost analysis, and provides OTT and CDN visibility that helps operators understand service origins, subscriber traffic patterns, and delivery inefficiencies. Kentik automatically labels internet traffic with CDN names and application name, type, and provider, giving operators a complete picture of traffic sources and the digital supply delivery chain.
Arbor claims some peering capabilities within Insight but lacks PeeringDB integration, broad market intelligence, connectivity cost tracking, and traffic cost intelligence.
Rich contextualization, dashboards, and integrations
Kentik lets teams enrich data with custom dimensions and business context — overlaying custom tags like physical locations, application names, and subscriber IDs onto network data. Teams can explore large historical datasets with powerful and unlimited filtering against the complete historical data set, and share dashboards and reports across engineering and leadership stakeholders.
Kentik also offers broad integrations and APIs, which makes it easier to fit into modern workflows instead of forcing teams to operate inside a closed monitoring island.
A better fit for organizations modernizing away from Arbor
For many operators, the decision is not “Can Arbor stop DDoS attacks?” It can. The real question is whether Arbor is the best platform for the next stage of network operations.
If your team needs unified SaaS delivery, broader cloud and internet visibility, integrated synthetics, open mitigation flexibility, and AI-driven investigation, Kentik is a compelling modern replacement for much of what buyers historically turned to Arbor for.
Many teams adopt Kentik without replacing Arbor on day one. A common approach is to start by replacing analytics and detection workflows first — adding flow analytics, cloud visibility, and synthetics for hybrid troubleshooting — then expanding DDoS detection and retiring legacy Arbor components as confidence grows. Kentik onboards incrementally so teams can prove value quickly before decommissioning legacy tooling.
Summary: Kentik vs NETSCOUT Arbor at a Glance
-
Unified visibility
- Kentik: One SaaS platform correlating flow, SNMP metrics, BGP routing, cloud telemetry, and synthetics.
- Arbor: Capabilities split across Sightline, TMS, Insight, nGeniusPULSE, and nGenius — each with separate management surfaces.
-
AI/ML
- Kentik: Natural-language investigation, AI-generated insights, and cross-domain root cause analysis via AI Advisor.
- Arbor: AI/ML limited to DDoS use case. No natural-language query, no generative AI, limited detection customization.
-
DDoS mitigation
- Kentik: Independent multi-vendor detection with RTBH, FlowSpec, and any third-party scrubbing integration out of the box.
- Arbor: Supports Arbor TMS (physical) or Arbor Cloud scrubbing only. Also supports RTBH and FlowSpec.
-
Cloud + hybrid
- Kentik: Integrated support for context-enriched VPC flow logs from AWS, GCP, and Azure.
- Arbor: Requires separate nGenius service (additional cost) for cloud monitoring.
-
Synthetic monitoring
- Kentik: Fully integrated inside-out, outside-in, and inside-inside testing with 300+ global agents.
- Arbor: nGeniusPULSE limited to inside-out testing only, not integrated with flow.
-
Data exploration
- Kentik: Search and query all context-enriched flow data without constraint or pre-configuration.
- Arbor: Requires pre-defining “Managed Objects.” Limited flexibility to filter and pivot; detailed data outside pre-defined objects may be summarized and lost.
-
Peering and cost intelligence
- Kentik: PeeringDB integration, connectivity cost monitoring, traffic cost intelligence, OTT/CDN labeling.
- Arbor: Some peering capabilities in Insight. No PeeringDB integration, no cost tracking.
-
Deployment + maintenance
- Kentik: SaaS-native with continuous feature delivery.
- Arbor: Appliance-based (physical or virtual), licensed “as a service.” Retention and scalability limited by hardware.
Other Notable NETSCOUT Arbor Competitors and Alternatives
Kentik is not the only option teams evaluate. Depending on whether the priority is DDoS mitigation, cloud scrubbing, or broader network intelligence, organizations may also consider the following Arbor competitors.
Radware (DefensePro / Cloud DDoS Protection)
Radware is a common Arbor alternative in DDoS-heavy evaluations, especially for buyers focused on detection and mitigation effectiveness.
- Strengths: Well known for DDoS mitigation through DefensePro, hybrid on-prem and cloud protection options, strong security orientation, and behavioral-based detection that adapts to attack patterns.
- Trade-offs: Fundamentally a security-first platform. Teams looking for broader network analytics, cloud observability, peering workflows, traffic cost intelligence, and unified traffic intelligence may still need additional tooling alongside Radware.
Cloudflare (Magic Transit)
Cloudflare is often considered when organizations want large-scale cloud-based scrubbing, internet-facing protection, and simplified deployment.
- Strengths: Massive edge scale through its global network, strong cloud-delivered DDoS protection via Magic Transit, and a relatively easy always-on operational model for public-facing services.
- Trade-offs: Not a full replacement for deep service provider traffic analytics, peering intelligence, or internal network observability workflows. Teams that need flow-based traffic engineering, historical investigation, or subscriber-level analytics will likely need a complementary platform.
Akamai (Prolexic)
Akamai’s Prolexic service is another option for organizations that want cloud-based DDoS scrubbing with global reach.
- Strengths: Dedicated scrubbing capacity with broad global coverage, well established among large enterprises and content-heavy organizations. Akamai’s broader portfolio also includes CDN, WAF, and edge security services.
- Trade-offs: Strength is in mitigation and edge protection rather than deep network traffic analytics, flow-based visibility, or service provider intelligence workflows. Often deployed alongside — rather than instead of — a network analytics platform.
A10 Networks (Thunder TPS)
A10 is another vendor that appears in DDoS mitigation evaluations, especially where buyers want appliance or hybrid deployment models.
- Strengths: DDoS detection and mitigation through Thunder Threat Protection System (TPS), with support for complex network environments and traditional on-prem deployment preferences.
- Trade-offs: Analytics and observability story is generally narrower than what buyers get from a full network intelligence platform. Teams needing cloud visibility, synthetic testing, or AI-assisted investigation will need to look elsewhere.
Corero (SmartWall)
Corero is often evaluated by operators that want purpose-built DDoS protection and automated response for high-availability environments.
- Strengths: SmartWall provides real-time, always-on DDoS detection and mitigation with fast automated response and sub-second mitigation for volumetric and protocol-based attacks.
- Trade-offs: A DDoS specialist, not a broad observability platform. Teams seeking cloud visibility, synthetic testing, peering analysis, traffic cost intelligence, and AI-guided investigations will likely need additional tools.
FAQs About NETSCOUT Arbor Alternatives
What are the best NETSCOUT Arbor alternatives?
The best alternative depends on what you need to replace. If the goal is only DDoS mitigation, teams often evaluate vendors such as Radware DefensePro, Cloudflare Magic Transit, Akamai Prolexic, A10 Thunder TPS, or Corero SmartWall. If the goal is to replace Arbor with a broader platform for network analytics, DDoS detection, cloud visibility, synthetics, and AI-assisted troubleshooting, Kentik is one of the strongest options.
What is the difference between NETSCOUT Arbor and Kentik?
NETSCOUT Arbor is an appliance-based DDoS detection and mitigation stack delivered as separate components (Sightline, TMS, Insight). Kentik is a SaaS-native network intelligence platform that combines DDoS detection, traffic analytics, cloud visibility, synthetic monitoring, and AI-assisted investigation in one system. Arbor’s AI is limited to DDoS workflows; Kentik’s AI Advisor provides natural-language investigation across all telemetry domains. Arbor’s mitigation supports only Arbor TMS or Arbor Cloud; Kentik orchestrates with any third-party scrubbing service.
Is Kentik an alternative to Arbor Sightline, Arbor Insight, and TMS?
Kentik can replace much of the detection, analytics, and investigation workflow historically handled by Arbor Sightline and Arbor Insight. For mitigation, Kentik supports RTBH, FlowSpec, and orchestration with third-party mitigation services, which gives operators flexibility in how they modernize. Some teams replace a legacy Arbor stack outright, while others start by replacing analytics and detection workflows first and phase out Arbor components over time.
Is Kentik better than Arbor for service providers?
Kentik is designed for service provider and edge-centric use cases and goes beyond DDoS defense to include peering analytics with PeeringDB integration, OTT/CDN traffic intelligence, subscriber-level visibility, traffic cost analysis, and AI-assisted troubleshooting. For providers that need a unified platform across DDoS detection, traffic engineering, cloud visibility, and operational intelligence, Kentik offers a broader solution than Arbor’s componentized stack. See also: Kentik Service Provider Video Case Studies
Why do teams replace Arbor Insight?
Teams usually look for an Arbor Insight alternative because they want a more unified experience. Common reasons include SaaS delivery, faster exploratory analytics without pre-defined managed objects, integrated cloud visibility, richer contextualization, built-in synthetics, more open APIs, and AI-assisted workflows that go beyond DDoS operations.
What should service providers look for in an Arbor alternative?
Service providers should look for more than attack detection. The best platforms combine DDoS defense with real-time flow analytics, BGP and routing context, OTT/CDN intelligence, peering analysis with PeeringDB integration, cost intelligence, long-term historical data, flexible multi-vendor mitigation orchestration, cloud telemetry, and easy-to-share dashboards.
Does NETSCOUT Arbor include synthetic monitoring?
NETSCOUT offers synthetic monitoring through nGeniusPULSE, but it is limited to inside-out testing only and is not integrated with flow data. Buyers comparing Arbor alternatives often prefer platforms like Kentik that integrate synthetic monitoring — with 300+ global testing agents and inside-out, outside-in, and inside-inside testing — directly with traffic, routing, cloud, and DDoS workflows in one place.
Can I adopt Kentik without replacing Arbor on day one?
Yes. Many teams prefer a phased approach: start by adding flow analytics, cloud visibility, and synthetics for hybrid troubleshooting, then expand DDoS detection and retire legacy Arbor components as confidence grows. Kentik onboards incrementally (collectors and agents first) and correlates telemetry across domains so you can prove value quickly before decommissioning legacy tooling.
Learn More About Kentik as a NETSCOUT Arbor Alternative
NETSCOUT Arbor remains a respected name in DDoS protection, especially in service provider environments. But many teams evaluating Arbor alternatives are now solving a broader problem than attack mitigation alone. They need unified network intelligence across traffic analytics, cloud and internet visibility, synthetic monitoring, peering and cost optimization, and AI-assisted troubleshooting.
That is where Kentik stands out. Kentik combines modern SaaS delivery with fast data exploration, integrated DDoS detection and mitigation workflows, multicloud observability, synthetic testing, and service provider intelligence in a single platform.
To see how Kentik can help you consolidate legacy tools and modernize network operations, explore AI Advisor, Synthetic Monitoring, Peering and Interconnection, or learn more about DDoS protection and mitigation. You can also request a demo or sign up for a free trial to evaluate Kentik in your own environment.


