How ISPs & Managed Service Providers Can Offer DDoS Protection

Summary
As organizations increasingly rely on digital operations there’s no end in sight to the DDoS epidemic. That aggravates the headaches for service providers, who stand between attackers and their targets, but it also creates the opportunity to offer effective protection services. Done right, these services can deepen customer relationships while expanding revenue and profits. But to succeed, providers will need to embrace big data as a key element of DDoS protection.
How Service Providers Can Seize the Cybersecurity Opportunity

While Tier 1 communications providers have long made extensive cybersecurity capabilities part of their managed services portfolios, the offerings of Tier 2 telcos — hosting providers, ISPs, and MSPs — have typically been more limited. The recent dramatic rise in DDoS (distributed denial of service) threats, however, has given service providers of nearly every stripe the opportunity to offer protection services that can enhance customer relationships while growing revenue and profits. To do so successfully, service providers will need to embrace big data as a key element of powerful DDoS protection.
The DDoS Threat… and Opportunity
Recent years have brought the DDoS threat home in a way that makes it hard to ignore the risks. Back in 2014 — long ago in Internet time — 41% of organizations globally were hit by DDoS attacks, with three quarters of those (78%) targeted twice or more in the year. Far from dissipating over time, attacks have grown in severity and volume. Recent spectacular attacks include those against internet hosting company OVH, security researcher Brian Krebs, and, most famously, DNS provider Dyn, which resulted in outages at Twitter, Netflix, Amazon, and many other websites for hours.
As the threat grows, so to does the vulnerability. More and more businesses are investing in significant digital initiatives to fuel competitiveness, revenues, and profits, and more IT assets are being outsourced to the cloud. That makes both top- and bottom-line aspects of businesses more susceptible to DDoS disruption. Luckily, it appears that the leaders of all types of businesses and government agencies are finally realizing that their organizations could be next. Partly as a result, worldwide spending on information security (per Gartner) was $85 billion in 2015 and is growing at a compound annual growth rate (CAGR) of 9.3%, making a projected market size of $117 billion in 2019.
Big Data Enhances Accuracy
Most people think of DDoS protection simply as “stopping attack traffic,” and in a basic sense that’s true. In an increasingly competitive environment, however, it’s not enough for a service provider to offer just the basics. The first generation of DDoS protection services were based on products built solely around detection and mitigation appliances. Appliances are still necessary and relevant for mitigation because ASIC and Network Processor power is needed for deep packet inspection when scrubbing traffic. But there’s no longer any reason for detection to be trapped in first-generation technology.
Legacy detection appliances are severely constrained in their CPU, memory, and storage, which limits their ability to track high volumes of traffic data. They try to compensate by relying on manual configurations and resorting to a variety of computational shortcuts. But they nonetheless miss an unacceptably high percentage of attacks.
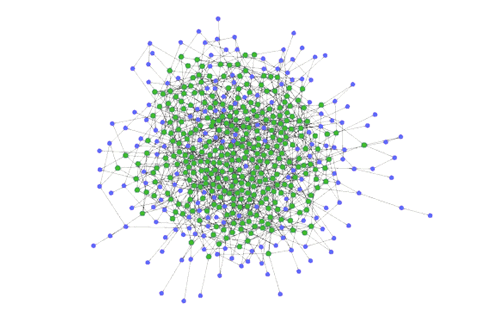
The key to solving this DDoS detection accuracy issue is big data. A distributed system that scales to network traffic volume can continuously scan network-wide data on a multi-dimensional basis without constraint. And it has the computational power to apply learning algorithms to baselining. The result is 30% more accurate DDoS attack detection. For more information on how big data helps accuracy, read our post on Big Data for DDoS Protection.
Analytics Enable Consultative Relationship
One of the chief advantages that telecom and hosting providers have is the fact that customers already entrust them with critical connectivity and infrastructure services. This trust places them in an ideal position to offer a highly consultative approach. Unfortunately, traditional DDoS systems are nearly devoid of real analytics. This means that to offer valuable data in the pre-sales, post-sales, or managed services phase of a customer relationship, service providers have to deploy a separate tool at additional cost.
That shouldn’t be the case, since customers can already send vast quantities of rich network telemetry — traffic flow records, BGP routing, and SNMP metrics — to the detection layer of a DDoS protection service. Big data helps by retaining all of that data in full detail, and making it possible to leverage it to advise customers with insights that add real value, cementing the trust relationship. For a glimpse at the kind of analytical power that big data provides, read our post DDoS Detection: Source Geography NetFlow Analysis.
Big Data That Works
Big data can mean many things, since there are a plethora of platforms, both open source and commercial, that promise the sun, moon, and stars to willing masochists. But most big data platforms aren’t fundamentally suited to real-time applications such as DDoS defense and network operations. The few that can be effectively adapted are extremely expensive. And no matter what home-grown option you choose, you have to develop and then maintain DDoS detection and network analytics capabilities. Nearly everyone who’s tried it has soon realized that it’s a painful and resource-intensive endeavor.
That’s why Kentik created a big data solution that’s purpose-built for network operations including DDoS protection, deep analytics, and network performance monitoring. Most providers will find Kentik Detect fast and convenient to deploy as a SaaS; you can sign on in less than 15 minutes, register your devices, and set up automated RTBH in under an hour. For service providers with data sovereignty, regulatory, or other requirements, Kentik Detect can also be set up on-premises.
Kentik Detect’s big data backend enables us to offer the industry’s most powerful and accurate DDoS detection, combined with integrated support for hybrid mitigation via RTBH and leading mitigation vendor solutions. One regional ISP that’s taken advantage of our superior detection — plus integrated support for Radware DefensePro — is PenTeleData; learn more by reading the case study.
For additional information about Kentik Detect’s DDoS protection capabilities, Read our solution brief to learn more about Kentik DDoS Detection and Defense. If you already know that you’re ready to try Kentik request a demo or start a free trial today.