Summary
Kentik and Cloudflare have a new integration. Read why and how we’ve expanded our partnership for on-demand DDoS protection.
The rolling thunder of cybersecurity warnings has built to a crescendo this year. According to HelpNetSecurity, cybercriminals launched over 9.75 million DDoS attacks in 2022. The Cloudflare Attack Trends 2022 Q1 Report published yesterday shows an alarming increase in application-layer DDoS attacks. And our own Doug Madory has been sharing analysis on the impact of cyberattacks, too.
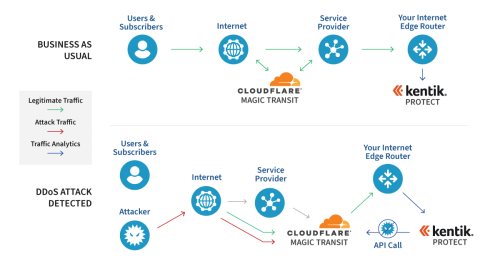
In May of 2020, Kentik and Cloudflare jointly announced that we’d be integrating Kentik Protect with Cloudflare Magic Transit. The success of this integration and growing customer interest has led us to strengthen that relationship. Starting today, the Cloudflare team will now be able to resell Kentik directly, offering customers the ability to buy and deploy a fully integrated on-demand DDoS mitigation solution.
The Kentik Network Observability Platform monitors our customers’ infrastructure and, when a DDoS attack is detected, activates Magic Transit DDoS protection. Cloudflare ingests all traffic directed to customer networks, filters out DDoS traffic at the edge, and delivers clean IP traffic to the customer, preventing adverse impact to users.
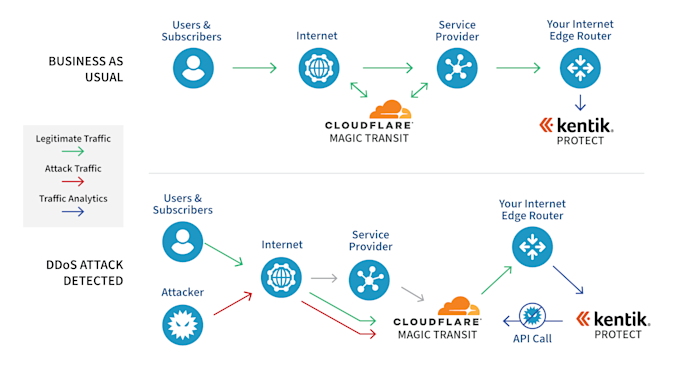
Cloudflare Magic Transit and Kentik Protect communicate via a REST API to trigger on-demand mitigation. Cloudflare Magic Transit has data centers in 250+ cities and over 120 Tbps of edge capacity, and can absorb and neutralize even the largest volumetric DDoS attacks, protecting any network from collateral damage and ensuring application availability for a business’ customers and users.
Advancing cybersecurity
Kentik Protect leverages powerful network analytics to deliver alerts and insights so you can mitigate DDoS attacks in real time. We have the most accurate and observable service for detecting volumetric and application-based attacks.

BGP monitoring
It’s not just DDoS attacks that concern those charged with protecting the network from cyber threats. Another threat that never seems to go away is BGP routing insecurity. In fact, just last month, Doug Madory posted about the latest BGP hijack of Twitter.
Although the recent successes in the adoption of Resource Public Key Infrastructure (RPKI) have helped to limit the impacts of BGP hijacks, monitoring is necessary to remediate any routing mishaps that can arise. BGP hijacks and leaks can misdirect internet traffic causing serious disruptions to application and service delivery.
Today’s BGP monitoring services rely almost exclusively on public data sources like RouteViews and RIPE RIS. However, Kentik is uniquely positioned to take BGP monitoring to the next level by extending those public data sources with thousands of private (anonymized) BGP feeds from our customers. The coverage offered by the BGP data used in our service will be unmatched by any BGP monitoring service in existence. We are currently investing considerable resources in building our BGP monitoring service to use this larger data set to detect routing anomalies like hijacks and route leaks, check RPKI statuses of routes, as well as offer an innovative visualization technique that will allow new types of analysis:
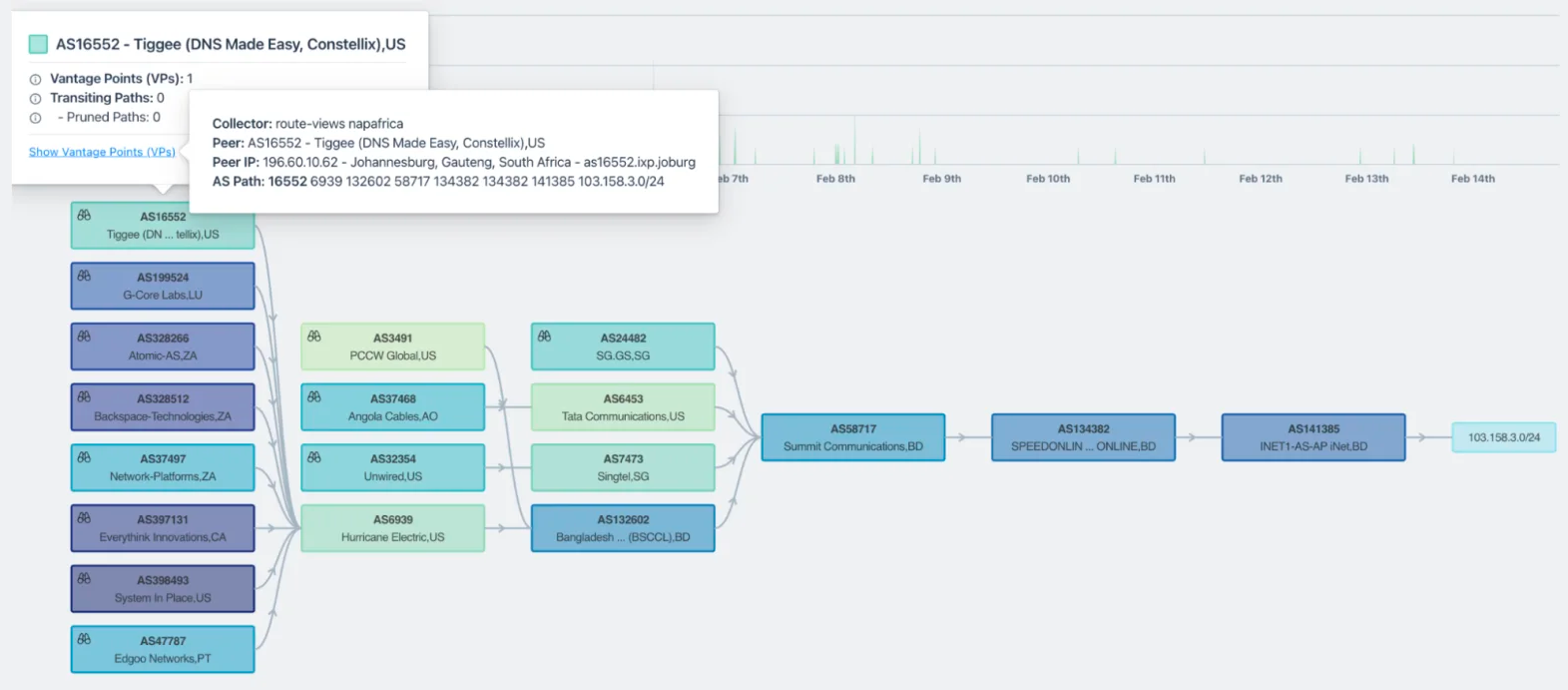
You can read more about our current BGP monitoring capabilities in this post.
Simplifying network security
Kentik and Cloudflare both aim to simplify network security for our customers. Magic Transit makes it easier for network professionals to know their network is protected. Now, we have extended that simplicity not only to detecting and mitigating DDoS attacks, but also to purchasing and integrating Magic Transit with Kentik. Combining Kentik’s BGP monitoring and DDoS detection with Cloudflare Magic Transit DDoS mitigation will go a long way to ensuring your infrastructure has the best protection possible.
We’ll be joining Cloudflare for the webinar DDoS attack trends and predictions for 2022 on April 28 at 10am PDT. For more information on the partnership and technical integration get in touch.