AWS Cloud Observability
Cloud shouldn’t be a black box. Get the right answer in seconds.
Fix and deliver apps in AWS
- Troubleshoot AWS workloads.
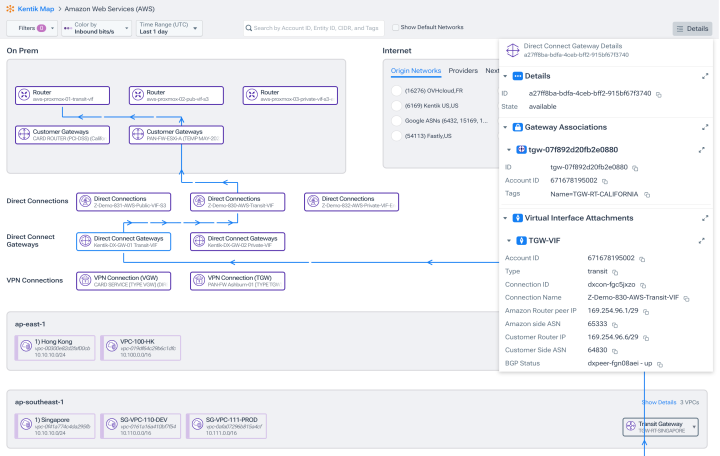
- Analyze traffic across Transit Gateways and Direct Connect, in AWS, and to and from your data center.
- Instantly understand how hybrid resources connect.
Optimize cloud network costs
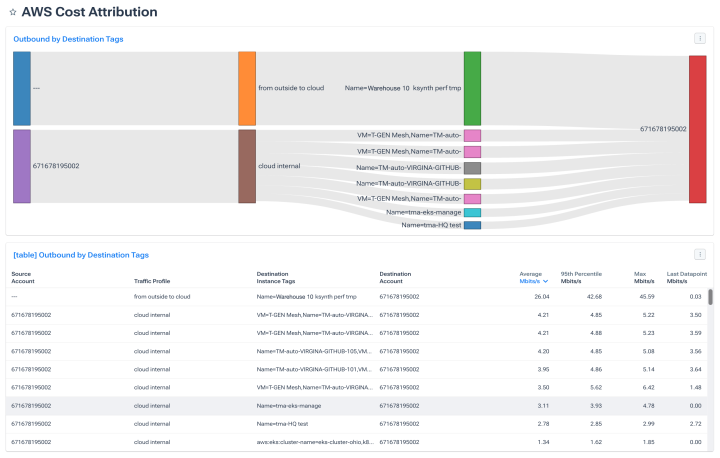
- Attribute cloud costs to business units.
- Reduce spend by optimizing private, inter-region, and inter-availability-zone routing.
- Instantly see the impact of AWS latency for data-driven cost negotiations.
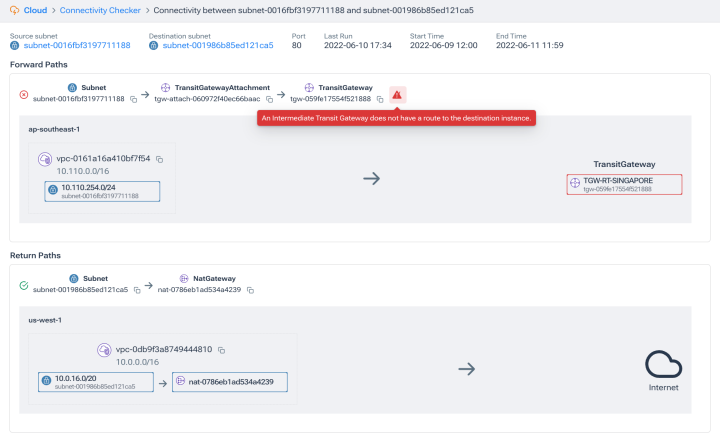
Pinpoint connectivity issues
- Breeze through investigations when you understand where connectivity between instances, subnets, and virtual private clouds is blocked — and how to fix it.
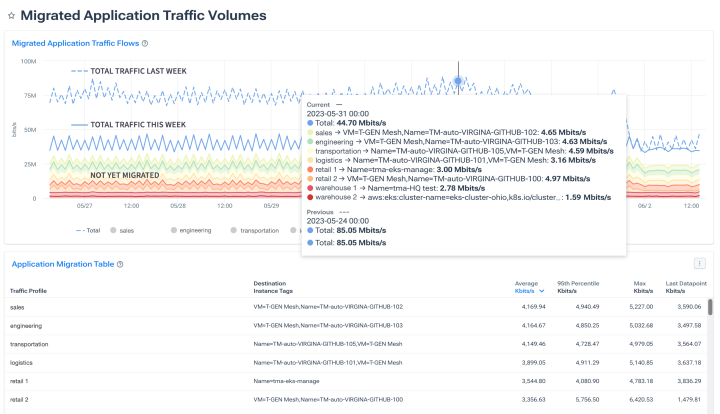
Ensure smooth migrations
- Plan migrations with understanding of baseline traffic and dependencies.
- Drive decisions on capacity, latency, geo-location, and policy with data before, during, and after migration.
Harden zero-trust cloud policy
- See cloud security policy in action.
- Find gaps in network security groups to restrict access to required ports and actors.
- Refine cloud policies as needed, quickly and easily.
Power your business with cloud networks
- Identify app consumption patterns to plan AWS capacity.
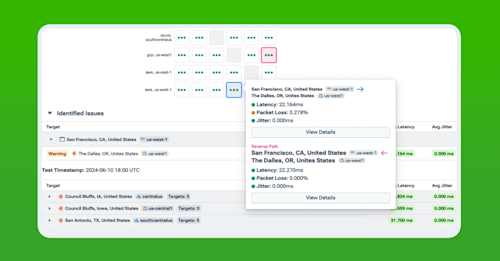
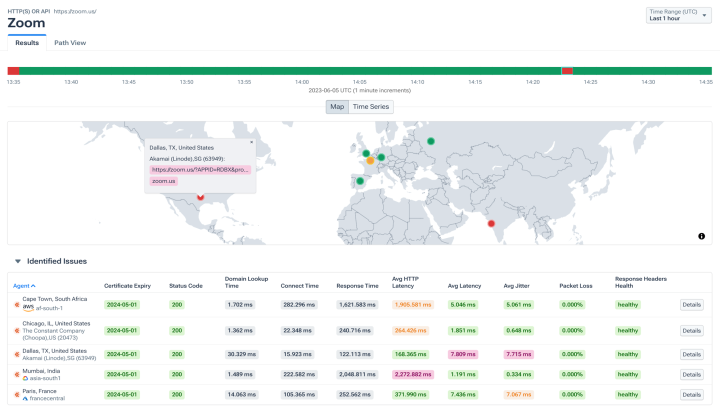
- Test connection performance between VPCs, VPN tunnels, and sites to understand latency and enforce SLAs.
Improve application performance
- Engineer traffic to isolate top bandwidth consumers and protect business-critical traffic.
- Find root causes of performance anomalies with easy QoS analysis.
Explore the platform
FAQs about Kentik for AWS
What AWS data sources does Kentik ingest?
Kentik ingests three core telemetry types from AWS: VPC flow logs (and Transit Gateway flow logs and Network Firewall logs), AWS metadata via API (VPCs, subnets, availability zones, security groups, route tables, gateways, Transit Gateways, and other infrastructure context), and metrics from connectivity services including AWS Direct Connect, AWS VPN, Transit Gateway, and PrivateLink. Together, these provide complete visibility into traffic patterns, topology, and performance across AWS environments. For Amazon EKS, Kentik also supports the eBPF-based Kentik Kappa agent for pod-level Kubernetes traffic visibility.
How is Kentik deployed on AWS?
Kentik is delivered as SaaS, so there’s no on-premises infrastructure to deploy. AWS setup involves three steps: enable VPC and Transit Gateway flow logs to a dedicated S3 bucket, create an IAM role granting Kentik read access to the bucket and AWS APIs, and configure a “cloud export” in the Kentik portal that connects to your AWS environment. Setup can be done manually or automated with the Kentik Terraform provider. Kentik is also available on the AWS Marketplace for procurement and billing through your existing AWS contract.
How does Kentik monitor traffic across AWS Transit Gateway and Direct Connect?
Kentik ingests Transit Gateway flow logs alongside VPC flow logs to provide unified visibility into traffic between VPCs, on-premises networks, and external destinations. For Direct Connect, Kentik collects connectivity metrics that show utilization, performance, and traffic distribution across each Direct Connect connection. The combination lets teams trace traffic end-to-end — from on-premises through Direct Connect, into the Transit Gateway, and across VPCs — in a single view, with the AWS metadata context that explains which resources are involved at each hop.
How do I monitor inter-Availability Zone and inter-region performance in AWS?
Inter-AZ and inter-region monitoring requires correlating VPC flow logs with AWS metadata (which AZs and regions each resource belongs to) and synthetic tests between locations. Kentik supports this by automatically tagging flow records with AZ and region information from AWS APIs, surfacing inter-AZ and inter-region traffic patterns in the Kentik Map, and running synthetic tests from agents deployed in different AWS regions to measure latency, loss, and reachability between them. This makes it possible to detect performance regressions on specific paths and attribute the cost of cross-AZ or cross-region data transfer to specific applications or business units.
How does Kentik help reduce AWS data transfer and egress costs?
AWS data transfer charges accumulate from inter-AZ traffic, cross-region replication, NAT Gateway processing, and egress to the internet — and most teams have limited visibility into which applications and traffic flows are driving the cost. Kentik analyzes VPC and Transit Gateway flow logs to surface the highest-cost flows, attribute traffic to specific VPCs, services, or business units, and identify suboptimal routing decisions (for example, traffic crossing AZs unnecessarily, or egressing through a more expensive path than needed). Teams use this data to optimize architecture, negotiate Direct Connect or AWS pricing with evidence, and reduce monthly data transfer spend.
How does Kentik handle Kubernetes networking in Amazon EKS?
For Amazon EKS, Kentik provides pod-level network visibility through the Kentik Kappa agent, an eBPF-based agent that captures container traffic without sidecar deployment overhead. Kappa surfaces pod-to-pod and pod-to-service traffic, including key performance indicators like retransmit rate and out-of-order packet rate, and correlates that traffic with the underlying VPC and AWS infrastructure context. This makes it possible to investigate microservice performance issues at both the Kubernetes layer and the AWS network layer in a single platform — useful when EKS performance problems turn out to have causes in VPC routing, security group rules, or cloud network paths.
What tools correlate AWS network performance with application metrics?
Effective correlation requires both data sources to live in environments that share time-aligned context — typically by integrating an APM platform (Datadog, New Relic, Dynatrace) that captures application metrics with a network intelligence platform that captures cloud network telemetry, BGP routing, and synthetic measurements. Kentik supports this by ingesting AWS flow logs, AWS metadata, and synthetic test data, then exposing the results through APIs and integrations that connect with major APM platforms — letting application teams trace performance issues from service symptoms back to AWS network root causes.
How does Kentik compare to AWS CloudWatch and other AWS native monitoring tools?
AWS CloudWatch and AWS native monitoring (VPC Flow Logs in CloudWatch, AWS Network Manager, Reachability Analyzer) are essential for AWS-specific operational visibility, but they’re scoped to AWS itself. Kentik complements AWS native tooling by providing cross-environment analytics — correlating AWS traffic with on-premises NetFlow, multi-cloud telemetry from Azure and GCP, BGP routing, and internet path data — and by adding capabilities AWS native tools don’t provide, including ingest-time enrichment with BGP and AS path metadata, flow-level forensics across hybrid environments, cloud egress cost analytics, and AI-driven investigation through Kentik AI Advisor. Most teams use both: AWS native tools for AWS-specific operations and Kentik for the cross-environment network intelligence that AWS native tools weren’t designed to deliver.
For more detail, see our article, CloudWatch Alternatives: Enhancing Multicloud Network Observability.