Summary
There has been a new development in The Mystery of AS8003.
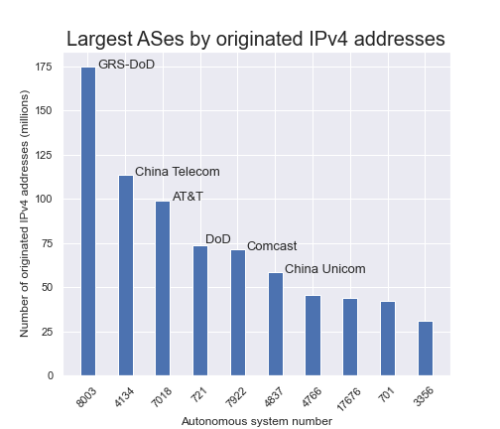
As you may recall, this was the AS number registered to a defunct company in Florida that appeared earlier this year in the global routing table announcing over 175 million IPv4 addresses belonging to the US Department of Defense.
Well, that just changed.
There has been a new development in The Mystery of AS8003.
As you may recall, this was the AS number registered to a defunct company in Florida that appeared earlier this year in the global routing table announcing over 175 million IPv4 addresses belonging to the US Department of Defense.
Well, that just changed.
At 17:05 UTC (1:05pm) on Tuesday, 7 September 2021, all but one of the 765 prefixes previously announced by AS8003 were moved to a new origin, AS749 belonging to the US Department of Defense.
However, despite the new origin (AS749) these prefixes are still routed exclusively through Hurricane Electric (AS6939) and traceroutes to the address space die at a router in Ashburn, Virginia (72.52.92.226, 100ge5-1.core2.ash1.he.net) as they did previously when AS8003 was the origin.
Old AS paths:
… 6939 8003
New AS paths:
… 6939 749
At the beginning of the day on 7 September 2021, AS749 wasn’t announcing any routes to the global internet. One can verify this fact in either Routeviews public data, or with the RIPEstat tool’s Routing History view for AS749. Curiously, Hurricane Electric’s invaluable public tool, bgp.he.net incorrectly shows AS749 announcing these prefixes for at least the past six months.

Earlier today, the Pentagon told the Washington Post:
“The Department of Defense has transitioned the advertisement, or announcement, of DoD Internet Protocol Version 4 (IPV4) addresses, previously advertised under Global Resource Systems LLC, to the DoD’s traditional operations and mature network security processes.”
If the DoD had transitioned these routes to be announced by the “DoD’s traditional operations”, I would have expected them to be transited via AS721 which is how virtually all of the DoD IP address space is routed on the internet.
So it would seem this DoD activity, which may be the world’s largest honeypot, simply swapped out AS8003 for AS749 in BGP without changing much else.
Once again as a final note: your corporate network may be using the formerly unused DoD space internally, and if so, there is a risk you could be leaking it out to a party that is actively collecting it. How could you know? Using Kentik’s Data Explorer, you could quickly and easily view the stats of exactly how much data you’re leaking to AS8003 (now AS749). May be worth a check, and if so, start a free trial of Kentik to do so.
Additionally, we’ve got a short video Tech Talk about this topic as well—see Kentik Tech Talks, Episode 9: How to Use Kentik to Check if You’re Leaking Data to AS8003 (GRS-DoD).
