One View to See Them All
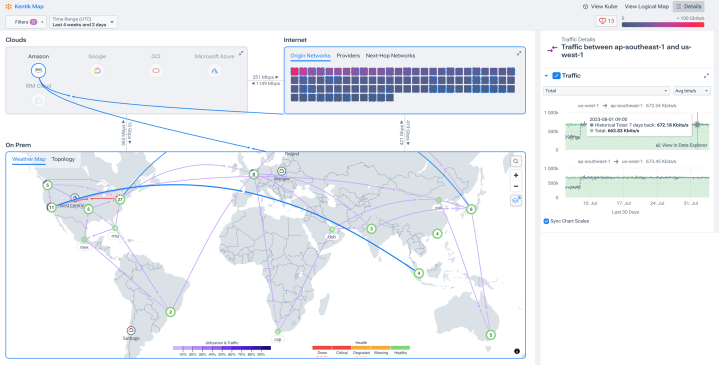
On prem, private cloud, public cloud — all in one view.
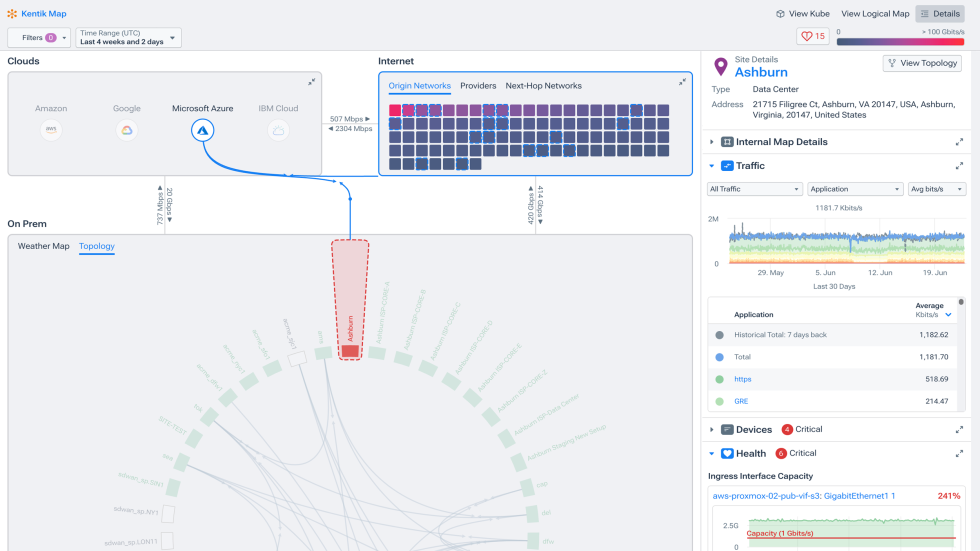
See how all networked resources nest within and connect to each other.
Understand path, performance, health, and security from on-prem to cloud.
Know whether the network is impacting application performance, and see how to fix it.
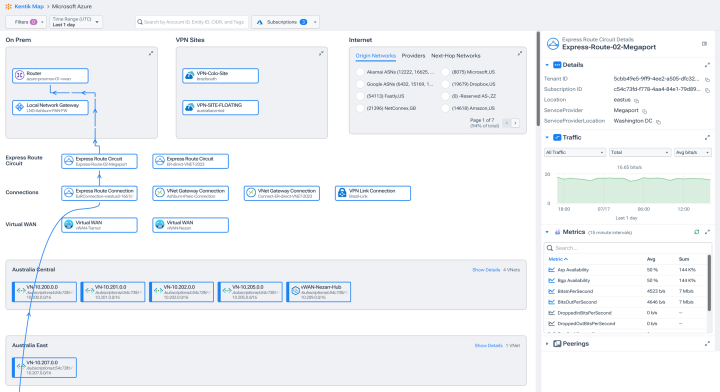
Visualize and investigate interconnect and multi-cloud topology
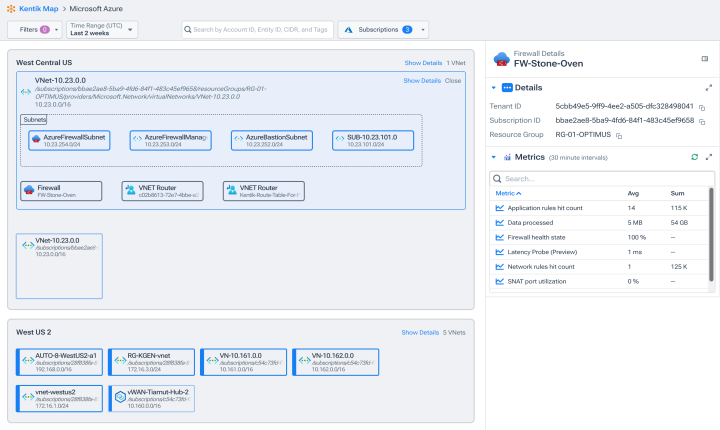
- See cloud topology across the major public clouds.
- Discover, manage, and troubleshoot Cloud Interconnect connections between your private and public clouds.
- Understand at a glance how cloud subnets and network infrastructure are designed and interconnected.
See critical detail with big picture context
- Easily access utilization, configuration, and performance data right from the map.
- Fix errors and optimize with rich metrics on cloud load balancers, firewalls, security groups, and application gateways.
- Get quick insight into SD-WAN, branch, VPN, private cloud, and intra-cloud connectivity.
Know where your data travels
- Quickly see denied and allowed traffic between VPCs, VNets, data centers, and the public internet.
- Verify with a visual that perimeter, security group, and Access Control List (ACL) rules match your security model.
- Visually detect anomalies in fast traffic explorations.

Make every decision with a current architectural blueprint
- Get always-up-to-date visualizations of your latest hybrid network infrastructure, automatically.
- Optimize ROI of moving resources to and from cloud with a complete picture of dependencies.
- Plan capacity, manage infrastructure, and onboard team members with a reliable source of truth.
“Kentik is actually showing you a visual representation of how your physical equipment connects via those virtual private connections in the cloud.”
Explore the platform
Network and Cloud Visualization FAQs
How do I visualize traffic distribution across regions and clouds?
Use a platform that maps your hybrid topology and lets you query traffic by cloud provider and region. Kentik Map visualizes cloud regions and interconnects, while Data Explorer and Insights let you break traffic down by cloud provider/region/subnet to understand distribution across clouds and geographies.
How do I map hybrid cloud and on-prem network topology in one view?
Use a live topology view that shows how cloud regions, VPCs/VNets, subnets, and on-prem sites connect, then overlay traffic and health so you can troubleshoot and plan from a single blueprint. Kentik Map provides a unified view into connectivity and traffic patterns across cloud and on-prem in one place. See: Kentik Map
How do I visualize and troubleshoot cloud interconnects like Direct Connect and ExpressRoute?
Start by visualizing interconnect topology and traffic between cloud networks and on-prem, then drill into specific connection paths when performance or reachability changes. Kentik Cloud Pathfinder helps troubleshoot cloud connection problems by showing paths between cloud resources and where connectivity breaks. See: Cloud Pathfinder
How can I view utilization and performance for cloud load balancers, gateways, and firewalls in context?
Use a map-first view that lets you click into cloud infrastructure components and see utilization, configuration, and performance signals alongside traffic flows. Kentik’s Cloud dashboards provide curated visualizations of cloud traffic and infrastructure across supported cloud providers. See: Kentik Cloud
How can I identify Internet-facing services and exposed paths across my hybrid environment?
Map cloud subnets, gateways, and load balancers alongside on-prem and interconnect links, then review which resources exchange traffic with the public Internet. Kentik’s hybrid map and cloud-traffic views help you find Internet-facing services and understand how traffic traverses interconnects and data centers. See: Cloud Visibility Tools
How do I see allowed vs denied traffic and quickly find what’s blocking connectivity between VPCs/VNets?
Use flow telemetry that includes accept/reject signals and correlate it with the relevant cloud security controls so you can see whether traffic is permitted and why it’s blocked. Kentik can trace blocked cloud traffic and identify the security group responsible to speed troubleshooting and audits. See: Understanding Network Traffic Blockages in AWS
How do I verify security group and ACL rules match my intended security model?
Compare intended segmentation to observed traffic, including rejected flows and unexpected cross-segment access, and review it in the context of security groups, ACLs, and perimeter controls. Kentik supports policy validation by analyzing allowed and denied traffic so teams can spot misconfigurations and tighten least-privilege enforcement. See: Cloud Security Policy Management
How do I detect anomalies in hybrid cloud traffic with visual context?
Baseline normal traffic patterns across sites, VPCs/VNets, and interconnects, then alert on unusual spikes, new paths, or unexpected communications. Kentik Insights provides automatic notices about anomalous and significant traffic behaviors to accelerate investigation. See: Insights
How do I plan cloud migrations and understand dependencies before moving workloads?
Start with an always-current blueprint of how services connect across cloud, on-prem, and interconnects, then evaluate which dependencies and traffic paths will be affected by moving a workload. Kentik supports migration planning by using traffic and dependency visibility to guide safer cutovers. See: Cloud Migration
Can Kentik monitor AWS, Azure, and Google Cloud networks in one view?
Yes. Kentik unifies visibility across AWS, Azure, and Google Cloud and ties cloud topology to traffic and connectivity data, so you can go from a global view to the exact VPC/VNet/subnet, interconnect, or gateway involved. This helps teams troubleshoot faster and keep a consistent operational picture as architectures change.