Why the New Normal in Cyberattacks Demands Network Intelligence


Summary
As cyberattacks evolve into “machine-speed” disruption campaigns that span cloud, identity, and network planes, traditional monitoring is no longer enough to protect modern enterprise infrastructure. Shifting to a network intelligence model, powered by real-time telemetry and AI-driven reasoning, enables security teams to detect weak signals and automate defenses before an incident becomes systemic.
Introduction
Recent cyber incidents are making one point unmistakably clear. Cyber disruption now unfolds across the network, identity plane, cloud services, endpoints, and internet edge at machine speed. In Poland, officials said they foiled an attempted cyberattack against the National Centre for Nuclear Research. They said there were indications the activity may have originated in Iran, while also warning that attribution could have been disguised. In the U.S., a medical equipment company said a cyber incident caused a global disruption to its Microsoft environment, while Nextgov reported employees’ phones were wiped, workers were prevented from accessing computers, and a pro-Iran hacking group claimed responsibility.
These two events are not identical, but they illustrate the same new reality. Some attacks are aimed at gaining footholds in sensitive environments before defenders can contain them. Others are designed to create immediate operational disruption across enterprise systems. Both compress the time available for human teams to detect what is happening, understand the blast radius, and respond with confidence. That is why the network has become more than infrastructure. It is now a core source of security truth and operational resilience.
The challenge is one of machine-speed attacks that require defenses to evolve beyond manual processes, with AI Advisor designed to reason across the full network context and guide immediate response. The solution is a platform for preventing attacks where possible, detecting attacks faster when they occur, and responding with richer, real-time network context.
The latest attacks are a warning: Disruption is the new normal
The lesson from the Poland and Stryker incidents is not limited to their sectors or geographies. It is that modern cyber campaigns increasingly target the systems that keep organizations operating. In the Poland-style scenario, anomaly detection matters because it can help catch reconnaissance, initial intrusion attempts, and lateral movement before an attacker reaches critical assets. In the Stryker-style scenario, anomaly detection matters because it can expose enterprise-wide disruption patterns, identify which assets are affected, and help teams understand whether the problem is local, regional, or systemic.
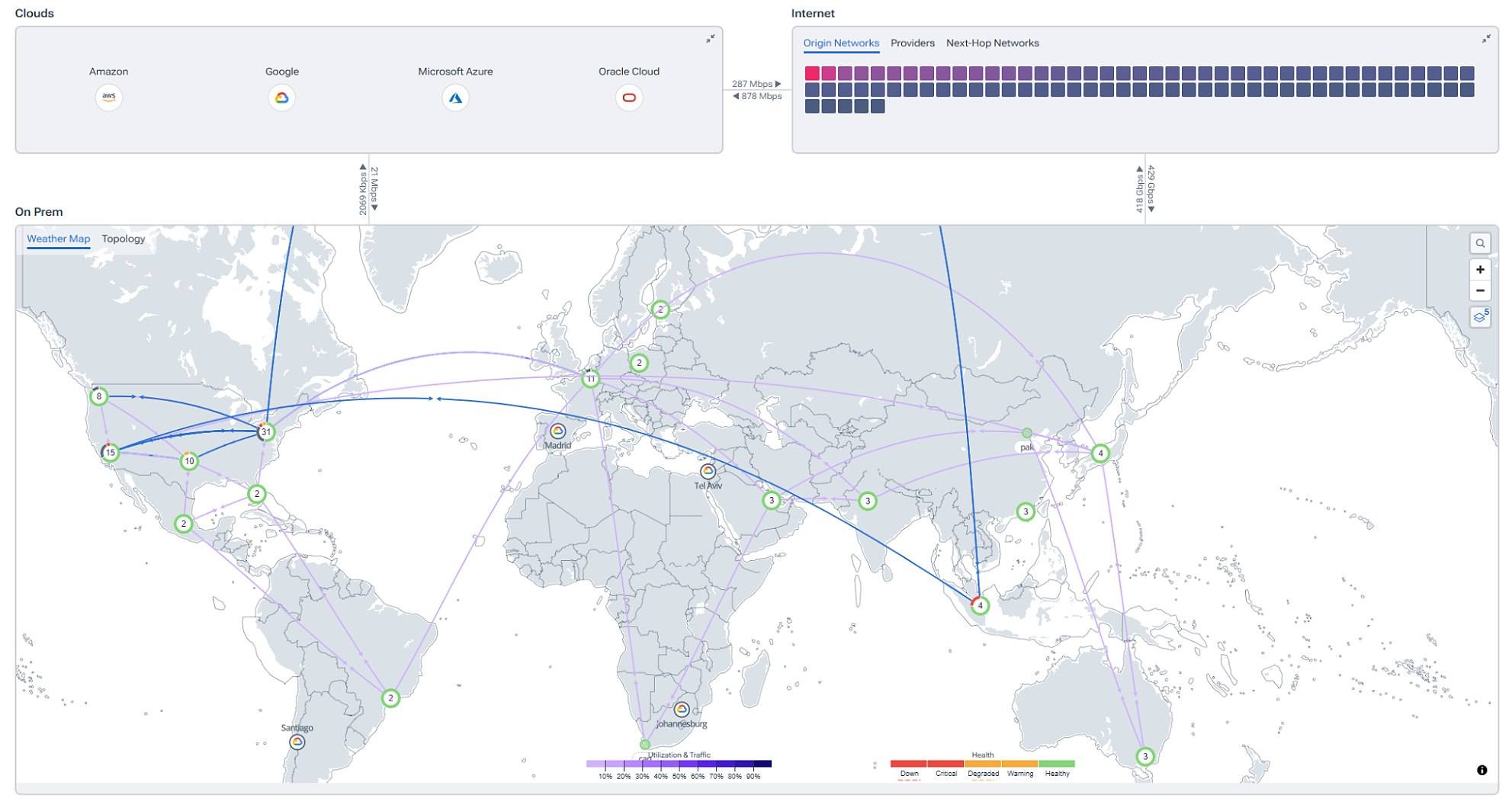
This is where many organizations still have a blind spot. They treat the network as a transport layer and security as a separate function. That model has become outdated. When disruption crosses cloud, WAN, edge, SaaS, and on-premises environments, the network becomes the one place where defenders can often see the earliest weak signals and the broadest operational consequences. The Kentik Network Intelligence platform is the solution for modern infrastructure teams, built to unify telemetry across all networks and automate mitigation when attacks are detected.
Why machine-speed attacks expose the limits of human-scale response
Attackers are no longer relying solely on human operators, and autonomous AI attacks operating at machine speed demand a security model that goes beyond manual processes. The risk is not only more attacks. The risk is faster reconnaissance, faster exploitation, and faster adaptation once inside the environment.
That shift changes what leaders should expect from their operational tooling. A human team cannot manually pivot across flow data, routing changes, cloud dependencies, device metrics, and synthetic checks fast enough during a live incident. This is especially true when an incident may involve both classic network behavior changes and platform-level disruptions, such as when identity or collaboration systems become impaired.
Why traditional monitoring leaves dangerous gaps
Traditional monitoring often produces alerts without enough context to answer the questions that matter most. What changed? Is this malicious, misconfigured, or merely unusual? Which assets are affected? How far has the issue spread? In a Poland-type event, defenders may need to determine whether suspicious traffic is recon, a failed intrusion, or the start of lateral movement. In a Stryker-type event, they may need to determine whether a disruption is isolated to endpoints, tied to identity infrastructure, or indicative of a broader control-plane compromise.
Prevention and response both improve when teams work from deeply enriched network data across data center, cloud, and container footprints. Traffic analysis establishes a baseline for what normal looks like, and anomaly detection then identifies deviations from those normal patterns before they escalate into larger attacks. Threat-feed enrichment adds additional value by identifying flows associated with command-and-control servers, malware distribution points, phishing sites, and other known threats.
This is an important distinction for security leaders. Pure DDoS detection is highly valuable when the attack involves flooding, protocol abuse, or service exhaustion. DDoS defense is designed for exactly that use case, using machine learning-based traffic profiling, attack visualization, and automatic mitigation actions such as RTBH, Flowspec, and external mitigation services. But many modern incidents are not pure DDoS events. They are blended disruption campaigns, where anomaly detection and full-context network intelligence become just as important as flood detection.
What network intelligence adds that security teams actually need
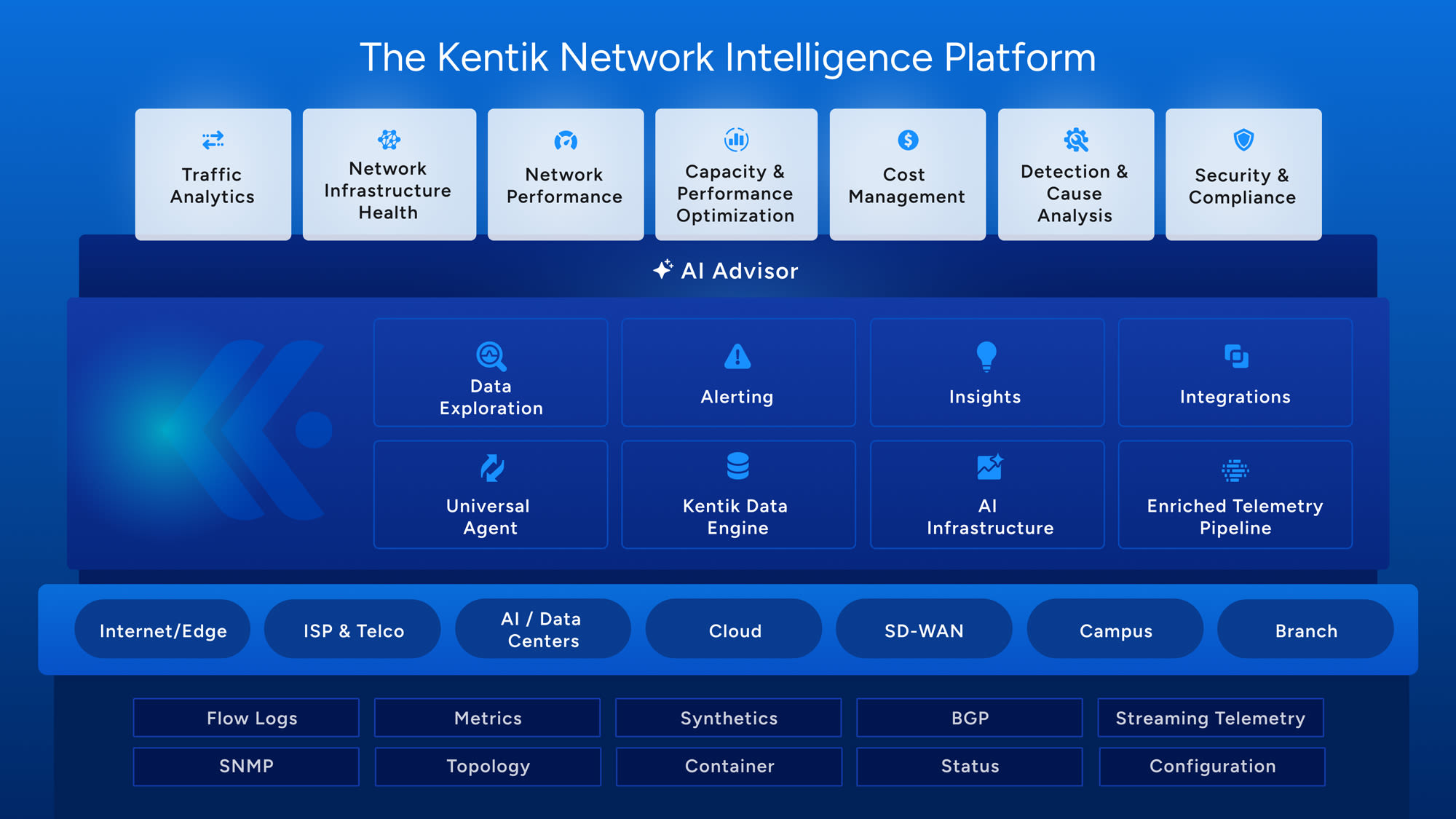
What security teams need now is not simply more telemetry. They need network intelligence. That means the ability to collect telemetry from critical networks and forwarding elements, visualize a unified view across owned and unowned environments, query all telemetry quickly, and retain rich historical data for accurate troubleshooting and forensics. The Kentik Network Intelligence Platform provides these capabilities directly, including broad telemetry collection, universal data exploration, real-time visualization, and long-term retention of raw data.
In practical terms, this changes defensive posture in three ways:
- Being proactive. Using policy verification, traffic monitoring, integrated threat feeds, anomaly detection, and proactive threat hunting to reduce the likelihood of a full-blown attack before it happens.
- Detecting and understanding attacks faster by correlating enriched network context across clouds, data centers, edge, SaaS, WAN, and SD-WAN.
- Response and post-incident investigation with real-time visibility and historical forensics.
This matters because the network often reveals both the earliest indicators and the widest blast radius. Abnormal outbound flows, suspicious destinations, unexpected geographic traffic, sudden path changes, or unusual service-to-service patterns can all provide clues that security teams can act on before disruption becomes systemic. This is supported by anomaly detection, real-time enrichment, and threat hunting guidance that aligns closely with these needs.
How Kentik helps prevent, detect, and respond faster
The Kentik Network Intelligence Platform helps teams stay ahead of attacks by turning network telemetry into actionable insight. With baseline traffic monitoring, teams can quickly understand what normal looks like and spot abnormal behavior before it escalates. Threat-feed enrichment, anomaly detection, and proactive threat hunting add another layer of context, helping surface indicators of compromise and expose weaknesses that might otherwise go unnoticed.
When an incident unfolds, speed and clarity matter. Kentik gives teams real-time visibility across cloud, data center, WAN, edge, and internet paths, along with the context needed to understand what changed, what is affected, and where to focus first. That accelerates investigation and shortens the path to root cause when every minute counts.
For response, Kentik supports DDoS-specific workflows with machine learning-driven traffic profiling and automated mitigation, while also feeding enriched network intelligence into SIEMs and other downstream systems through Firehose and additional integrations. The result is a faster, more coordinated response across network and security operations.
This is why the network should be treated as the first line of defense, not the last place teams look after an alert has already fired. It is where teams can see exposure, abnormal behavior, and operational impact together, in the full context of how the business runs.
Why AI Advisor matters when seconds count
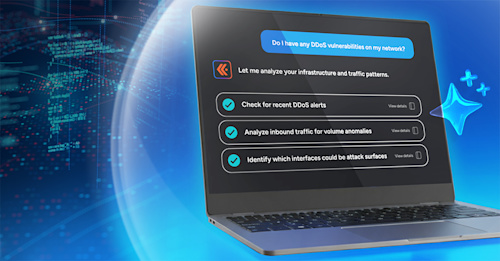
AI Advisor is an advanced AI agent that acts as a network intelligence partner, guiding triage, troubleshooting, and remediation suggestions through natural language interaction. It can interpret questions, make a plan, explain its reasoning, and accelerate incident response by reducing the need to manually query multiple tools.
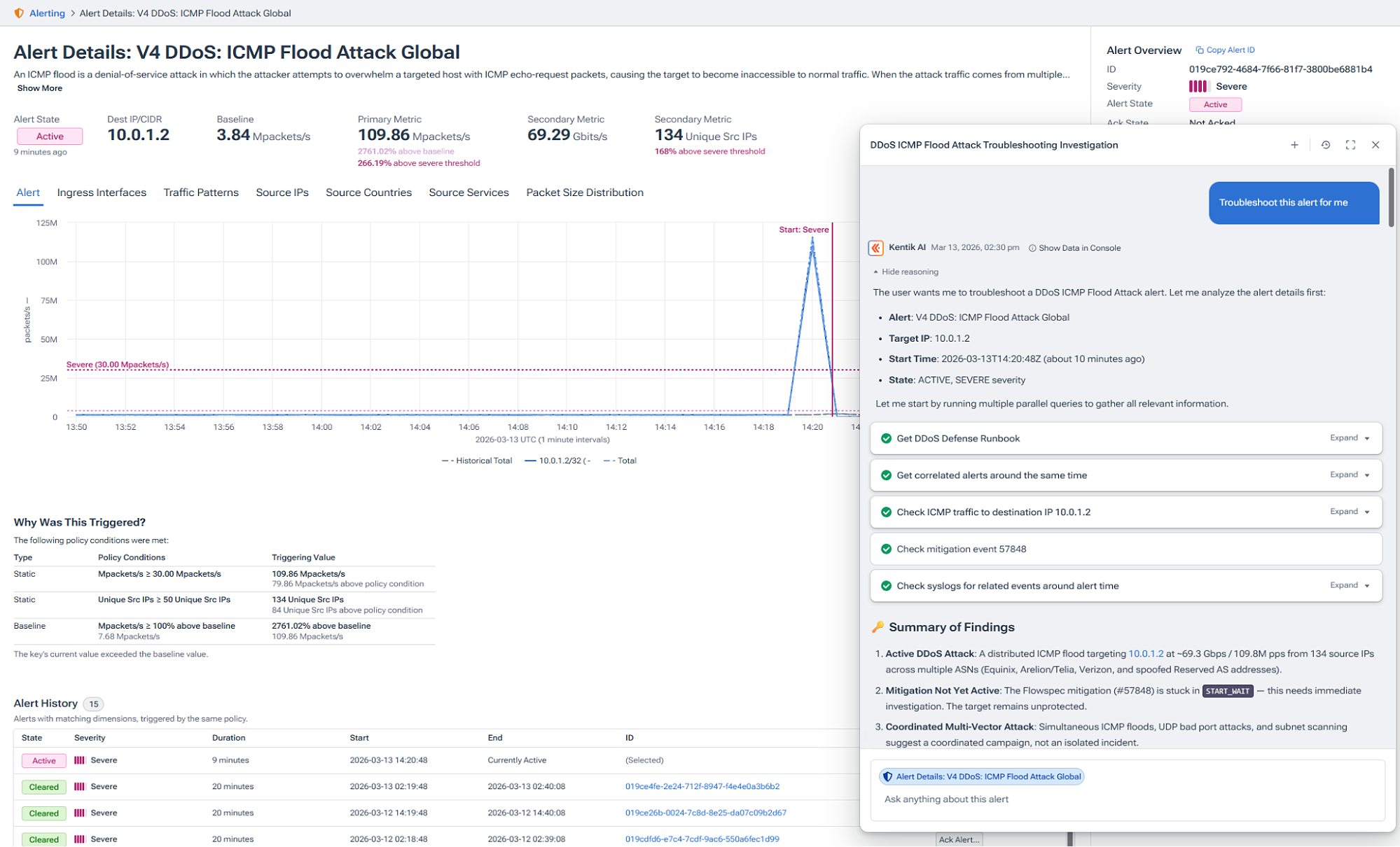
AI Advisor can be tailored with Runbooks and custom network context, so investigations can follow predefined diagnostic steps and take account of site naming, architecture, addressing conventions, maintenance windows, critical applications, and operational procedures. That matters in security because consistency and context reduce human error during high-pressure investigations.
In the new normal of cyber attacks, that combination of broad telemetry, network intelligence, and guided AI reasoning is increasingly important. It gives teams a way to move at a pace that better matches the attacks they are defending against.
Your response to the new normal
The latest incidents are a wake-up call, but the underlying lesson is larger than any single headline. Cyber disruption is now a resilience issue that unfolds across networks, identities, cloud, endpoints, and the internet edge. Defenders need to identify weak points before attackers exploit them, detect abnormal traffic and threat indicators quickly, and respond with full context. That is the case for treating network management and operations as a means of making the network a cyber-resilient asset.
The Kentik Network Intelligence Platform unifies telemetry, enrichment, visibility, investigation, and mitigation, with AI Advisor acting as a built-in force multiplier for security and network teams. By organizing investigations into clear steps, showing its reasoning, and providing interpretations grounded in data that teams can validate, it helps accelerate analysis while improving the accuracy, consistency, and quality of incident response and documentation. In a world of machine-speed attacks, the organizations that will respond best are the ones that stop treating the network as background infrastructure and start using it as an active source of cyber defense.
Related reading Learn more about Kentik Use Cases for Network Security & Policy, and AI in networking.