Protect Your Network from DDoS Attacks
Detect, analyze, and stop attacks in real time with AI-driven network intelligence.
Identify DDoS attacks and anomalies in real time with AI-driven traffic analysis.
Distinguish legitimate traffic spikes from attacks with confidence.
Automate mitigation with RTBH, Adaptive Flowspec, and integrated scrubbing partners.
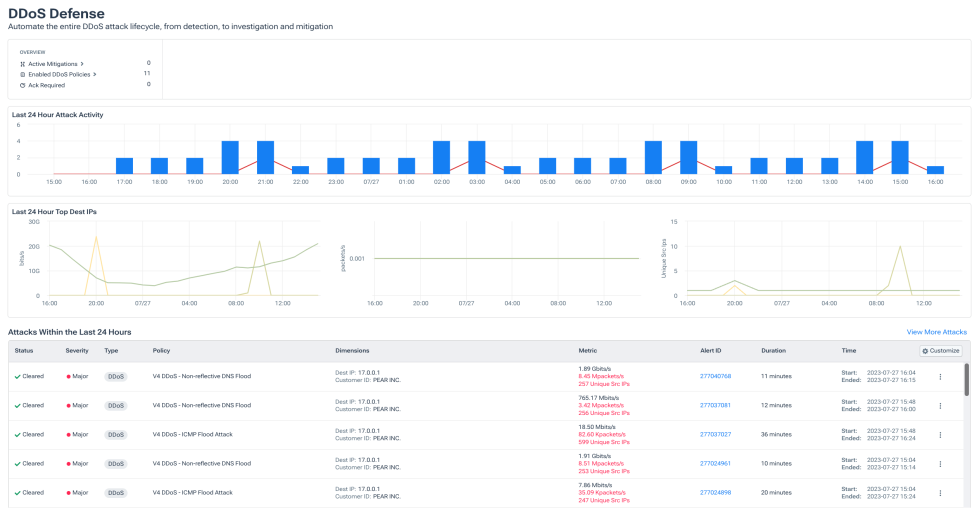
Real-time DDoS detection
- Quickly detect threats and find root causes with AI-assisted investigations.
- Identify malicious botnet traffic or communication with embargoed countries.
- Enrich detection with threat intelligence and global context feeds.
- Built for complex, high-scale networks.
Stop bad actors in their tracks
- Kick off automated mitigation with easy AI prompts and promptbooks.
- Respond with intelligence, such as diverting traffic using RTBH.
- Trigger Flowspec to filter, redirect, or rate limit traffic.
- Coordinate mitigation across teams and systems easily in one platform.
Harden your network security posture
- Understand any attack using customer-enriched forensic network data.
- Accelerate investigations with AI Advisor to uncover new attack vectors.
- Export data to any SIEM seamlessly.
Confidently detect real attacks
- Avoid false positives and unnecessary mitigation.
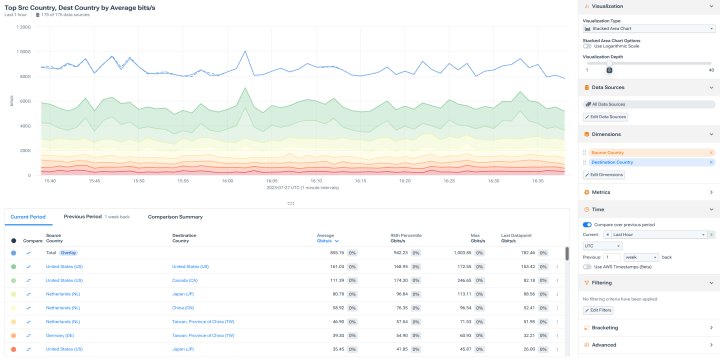
- Know where traffic is coming from when analyzing spikes.
- Pinpoint exact traffic sources, destinations, and protocols.

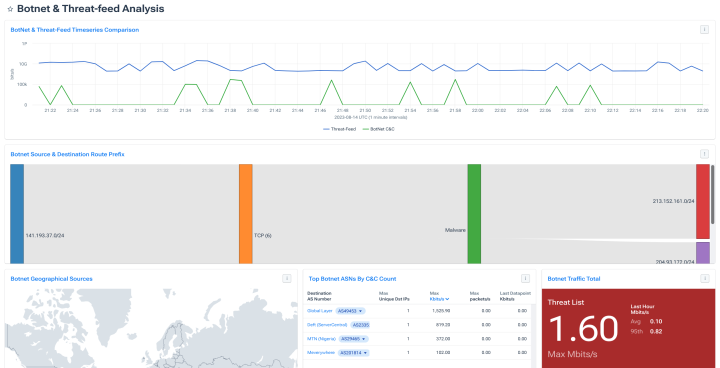
Protect against botnets
- Detect connections to known botnet command-and-control hosts on the internet.
- Track botnet behavior, routes, and geolocation trends over time.
- Alert and mitigate hyper-volumetric botnet attacks with AI Advisor

“In a DDoS attack you want to look at traffic volumes, but with Kentik we also can look at source IPs, AS numbers, and other metrics to see if it’s a distributed attack. This is so easy to do in Kentik.”
Explore the platform
FAQs
How does Kentik detect DDoS attacks differently from traditional tools?
Traditional DDoS detection relies on static thresholds that miss short-burst, low-volume, and multi-vector attacks — the exact tactics dominating the 2026 threat landscape. Kentik takes a different approach: it ingests and correlates massive volumes of flow data (NetFlow, sFlow, IPFIX), BGP routing information, SNMP metrics, and threat intelligence feeds in real time, then applies adaptive baselining and multi-dimensional analysis across your entire network. This means Kentik spots anomalies that blend into normal traffic — like reconnaissance probes or sub-saturating volumetric bursts — and distinguishes them from legitimate spikes such as flash sales or viral content. The result is field-proven accuracy gains of 30% in attack recognition compared to legacy approaches.
Is Kentik a DDoS scrubbing service?
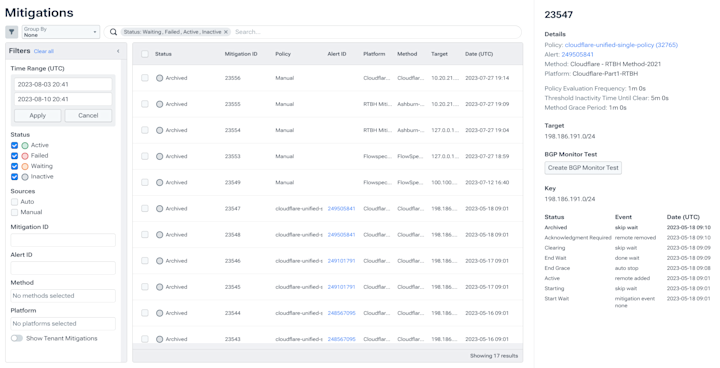
No — and that’s by design. Kentik is the network intelligence and decision layer that makes your entire DDoS defense stack faster and smarter. Kentik detects attacks with high accuracy, classifies what’s happening using enriched network context (flow + BGP + threat feeds), and automatically triggers the right response: RTBH, Flowspec filtering, or diversion to your scrubbing provider. Kentik integrates natively with Cloudflare, Radware, A10, and others. Scrubbing providers clean traffic; Kentik tells them when, what, and where to clean — and then verifies the mitigation is working. Many of the world’s largest networks use Kentik alongside their existing scrubbing infrastructure for exactly this reason.
How does Kentik AI Advisor help during a DDoS attack?
Speed determines how much damage a DDoS attack inflicts. Kentik AI Advisor lets your team investigate and respond using natural language — asking questions like “What are the top source ASNs hitting this destination IP in the last 10 minutes?” instead of building manual queries under pressure. AI Advisor summarizes attack characteristics, suggests appropriate mitigation actions, and can execute automated response workflows through promptbooks. This means even junior engineers on overnight shifts can perform expert-level DDoS triage, closing the skill gap that attackers exploit during off-hours. Organizations using AI-assisted workflows have shortened detection-to-mitigation from hours to minutes, reducing mean time to detect (MTTD), mean time to resolve (MTTR), and unnecessary escalations.
Can Kentik detect DDoS attacks across both on-premises and cloud environments?
Yes. Kentik provides a single platform for DDoS detection across data centers, public clouds (AWS, Azure, GCP, OCI), and the internet edge — wherever your traffic flows. It ingests cloud VPC flow logs alongside traditional on-prem NetFlow, sFlow, and IPFIX, correlates everything with BGP routing data, and applies consistent detection policies across all environments. This eliminates the need for separate DDoS tools per environment and gives you a unified view of attack traffic as it traverses hybrid infrastructure. Attackers don’t respect environment boundaries, and your detection shouldn’t either.
What is the business impact of faster DDoS detection and response?
Industry research shows that 49% of organizations lose $100,000 or more per hour of downtime during a DDoS attack, and most take over an hour just to detect an attack — with another hour or more to respond. Every minute you shave off that timeline directly reduces financial exposure. With Kentik’s always-on monitoring, adaptive baselining, and automated mitigation triggers, organizations have compressed detection-to-mitigation from hours to minutes. Beyond direct downtime savings, faster DDoS response protects SLA commitments, prevents customer churn, reduces incident response labor costs, and stops attackers from using DDoS as a smokescreen for data exfiltration or ransomware deployment.
How does Kentik use BGP data to improve DDoS detection?
BGP routing intelligence gives Kentik context that flow-only DDoS tools lack. During an attack, Kentik correlates traffic anomalies with routing changes — detecting, for example, when a traffic shift is caused by a BGP hijack redirecting flows through an adversary’s network versus a legitimate routing update. Kentik also uses AS path analysis and BGP community tags to identify upstream sources of attack traffic, enabling smarter mitigation decisions like selectively black-holing traffic from specific ASNs rather than dropping everything. This routing-aware approach is especially valuable for service providers, enterprises with complex peering arrangements, and any organization where understanding why traffic patterns changed is as important as knowing that they changed.
How does Kentik compare to Cloudflare or Akamai Prolexic for DDoS protection?
They solve different parts of the problem. Cloudflare and Akamai Prolexic are edge-mitigation and scrubbing services — they absorb and clean malicious traffic at massive scale. Kentik is the network intelligence layer that works alongside these services to make your overall DDoS posture more effective. Kentik provides deep traffic visibility, accurate attack classification, and automated orchestration that tells scrubbing services when to activate, what traffic to target, and then verifies mitigations are working as expected. Many organizations — including some of the world’s largest service providers and digital platforms — run Kentik together with Cloudflare or Akamai because the combination of mitigation capacity plus network-wide intelligence is stronger than either alone.
Can Kentik help detect botnet activity and other security threats beyond DDoS?
Yes. The same network telemetry Kentik analyzes for DDoS detection also reveals broader security threats. Kentik enriches flow data with IP reputation feeds — including Spamhaus — to identify connections to known botnet command-and-control servers, malware distribution points, and phishing infrastructure. It can flag potential data exfiltration through unusual outbound traffic patterns and detect shadow IT or unauthorized cloud services on your network. Kentik also provides RPKI analysis to help validate routing security and identify potential BGP hijacks. This means your investment in Kentik for DDoS protection simultaneously strengthens your broader network security posture — one telemetry platform serving both NetOps and SecOps teams.
How does Kentik automate DDoS mitigation responses?
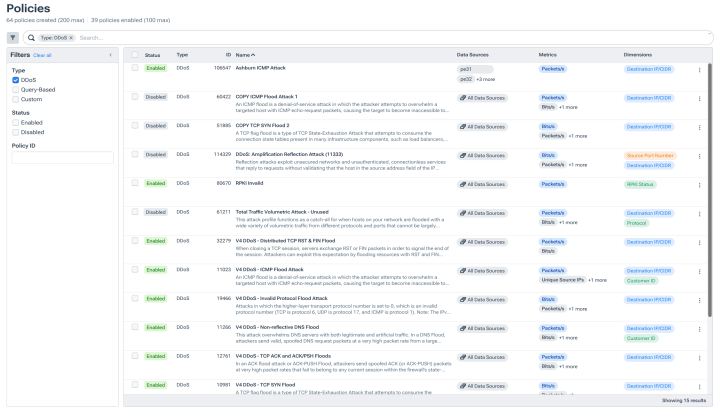
Kentik supports multiple automated mitigation methods that can be configured for fully automatic or human-in-the-loop execution. RTBH (Remotely Triggered Black Hole) drops all traffic to a targeted IP at the network edge — fast and effective for volumetric floods. Adaptive Flowspec applies granular BGP-based filters that rate-limit, redirect, or block specific traffic by protocol, port, or source — surgical enough to stop an attack without collateral damage. Scrubbing provider integration automatically signals partners like Cloudflare, Radware, or A10 to begin cleaning traffic via native API integrations. AI-assisted promptbooks through Kentik AI Advisor can guide or execute mitigation workflows using natural language, compressing response time from minutes to seconds. Mitigation policies can be customized per destination, attack type, and severity.
What DDoS attack types can Kentik detect?
Kentik’s adaptive detection engine covers the full spectrum of modern DDoS attack types, including volumetric floods (UDP, ICMP, DNS amplification), protocol and state-exhaustion attacks (SYN floods, fragmented packets), reflection and amplification attacks (NTP, memcached, CLDAP, SSDP), hyper-volumetric multi-vector campaigns that combine techniques simultaneously, and low-and-slow attacks designed to fly under traditional threshold-based detection. Kentik provides pre-built alert policy templates for common attack signatures that you can clone and customize, while its adaptive baselining catches novel attack patterns that don’t match any known signature. Because Kentik sees your full network context — not just a single link or appliance — it detects distributed attacks that appear normal at any single observation point but are clearly anomalous in aggregate.