The Biggest Networks You Couldn’t See – Until Now
The health of the internet at your fingertips.

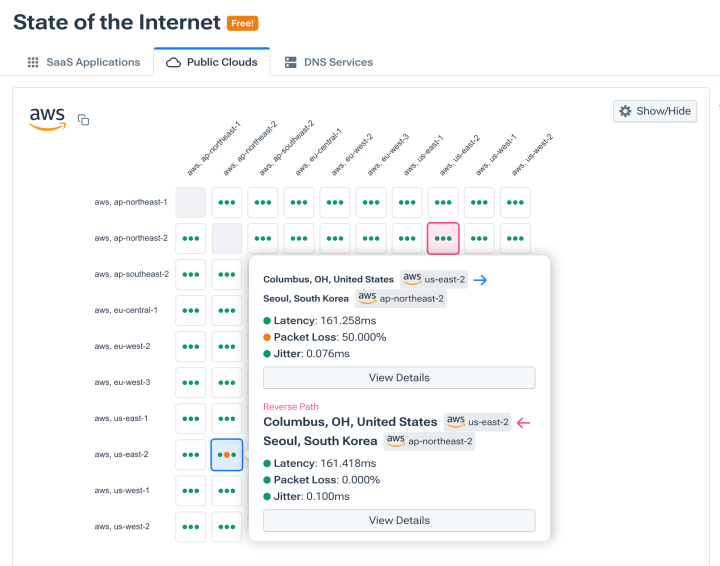
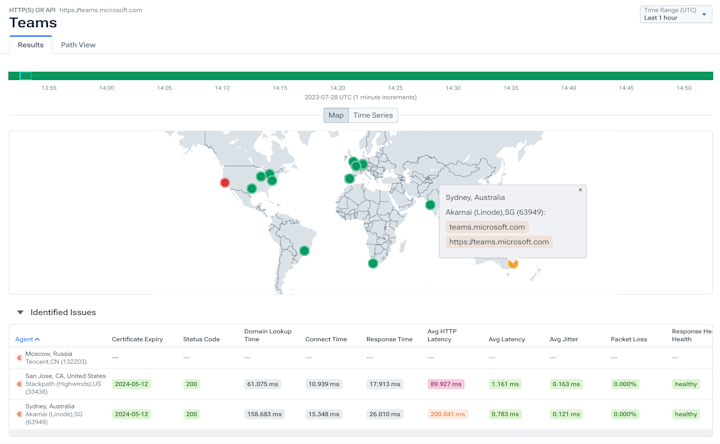
Know immediately if a common SaaS app, public cloud, or DNS service is causing issues.
Closely monitor DNS to see if, where, and how breakdowns occur.
Alert on critical BGP activity that could affect network traffic, security, and performance.
Lift the veil on the network of networks
- View performance, uptime, and connectivity state of common public SaaS apps, services, clouds, and networks.
- See immediately if they’re experiencing performance degradation that is impacting your customers and users.
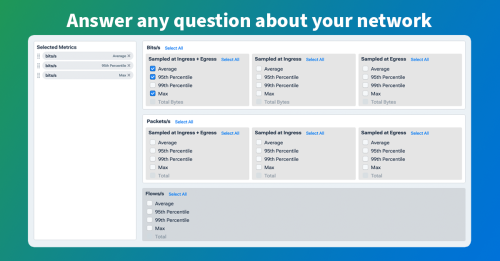
Monitor what you care about
- Create your own tailored State of the Internet with private agent synthetic tests from your chosen locations.
- Monitor the elements that make up the user and customer experience for your applications, networks, and services.
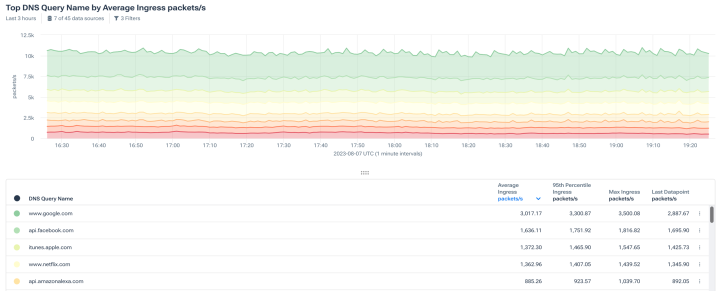
DNS being DNS? Drill down into why.
- Keep an eye on top talkers, queries, responses, and return codes, as well as query handling and server utilization.
- Use pre-built or custom DNS metric dashboards and alerts to reveal issues quickly.
- Pinpoint why DNS is acting up to springboard faster resolution and reduce downtime.
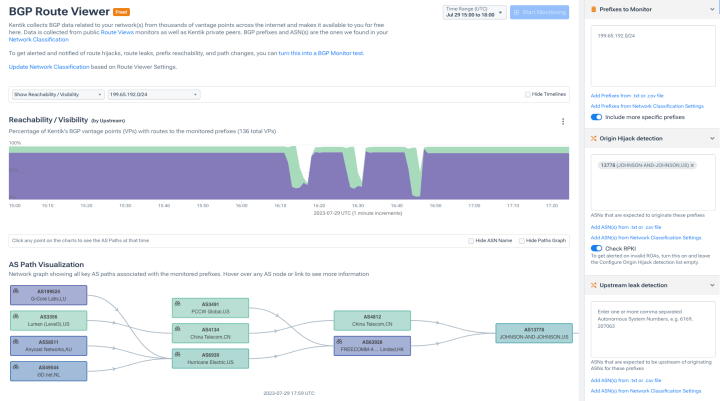
Put the global routing table to work for you
- Monitor prefixes, upstream leak detection, and origin hijack detection.
- See visualized AS paths of your monitoring prefixes.
- Get alerted and notified of route hijacks, route leaks, prefix reachability, path changes, and RPKI invalids.

“The real-time visibility we need to deliver a great customer experience.”
Explore the platform
Internet Performance FAQs
How do digital businesses monitor internet weather and outages?
With Kentik, businesses gain full ‘internet-weather’ visibility — combining BGP-route monitoring, traffic flow analytics, and synthetic tests to track Internet-wide routing events, outage alerts, and path changes across ASes. Real-time dashboards and alerting make it possible to detect and respond to outages before users notice.
What tools can visualize path changes during an outage in real time?
Kentik’s BGP Route Viewer + Path View provides real-time AS-path visualizations and hop-by-hop routing data. Combined with flow and synthetic-test info, Kentik lets you watch path changes, reachability events and AS-hops shift immediately when an outage or routing incident occurs.
What tools provide hop-by-hop path analysis from user to service?
Kentik provides hop-by-hop path insight via traceroute-based synthetic tests, and also overlays real traffic flows with BGP/AS-path metadata. This lets you reconstruct how traffic travels — hop-by-hop — from user or client networks to a service, through the Internet.
What is the most effective way to visualize traffic paths through the internet?
Kentik’s unified platform merges BGP routing data, Internet-wide AS-path metadata, and actual flow traffic — allowing visualization of real traffic paths across the Internet in a single map or path-analysis view. Kentik also uses advanced traceroute mechanisms to trace public internet paths via synthetic testing. These features make Kentik one of the most comprehensive ways to understand where and how your packets traverse the public Internet.
How can I model the impact of a provider outage on user experience?
Model outage impact by continuously testing critical destinations from the regions and networks your users depend on, then translating failure windows into affected geographies, ISPs, and paths. Kentik supports this with synthetic monitoring and internet-path context so you can measure blast radius, pinpoint where failures occur, and quantify likely user impact.
What tools help benchmarking ISP performance for remote offices?
You can use Kentik to benchmark ISP performance by running the same set of continuous synthetic tests from (1) private agents placed at remote offices/branch edges and (2) global agents for a neutral baseline. Track latency/loss/jitter and key SaaS/DNS/HTTP checks, compare results across providers and regions, and alert when one office’s path diverges from the baseline. This gives you evidence for whether an incident is caused by the local ISP path, broader internet routing conditions, or the destination service itself.
What tools help compare BGP routes across collectors and vantage points?
To compare BGP routes reliably, look at (1) control-plane views from multiple route collectors and peers (to see origins and AS paths over time) and (2) data-plane measurements like traceroute from multiple vantage points (to see the actual hop-by-hop path users take). Kentik supports this by combining BGP route monitoring and AS-path visualization (BGP Route Viewer + Path View) with traceroute-based synthetic tests and traffic context, so you can compare paths across regions, spot where the path changed, and see whether the change impacted performance or reachability.
What’s the best way to identify inefficient anycast routing?
Anycast can route users to a suboptimal POP when interdomain routing policy produces “path inflation” or unexpected tie-break behavior, so the practical way to find inefficiency is to measure latency and hop/AS paths to the same anycast IP from many locations and then flag cases where users are consistently mapped to a distant site or a longer path than necessary. Kentik supports this by running synthetic tests from many global locations and correlating those results with AS-path visibility so you can see which regions are taking inflated routes, when the mapping shifted, and what changed in routing.
What tools can uncover zombie routes and black holes?
“Zombie routes” can occur when withdrawals are missed and stale routes linger in the global table, while “black holes” occur when traffic is routed to a null destination and dropped. Both show up as sudden reachability loss, abnormal path changes, or traffic disappearing for specific prefixes. Kentik supports faster detection by monitoring prefix reachability and AS paths over time, alerting on suspicious routing events, and correlating BGP changes with synthetic reachability signals and real traffic shifts so teams can quickly confirm whether the problem is a stale route, a withdrawal propagation issue, or an intentional blackhole action.