AI that thinks and works like you do
- Interprets natural language requests and reasons through complex, multi-step investigations, just like an engineer.
- Acts autonomously to run queries across all your network telemetry.
- Step-by-step logic and transparent data provide validity to reached conclusions.
- Get clear, concise, expert advice and actionable recommendations.
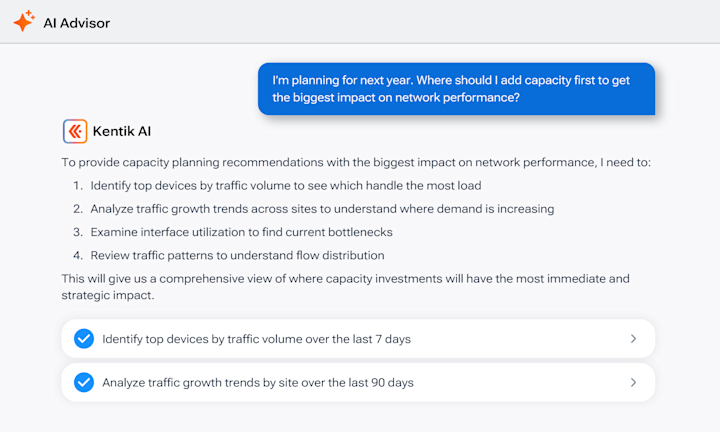
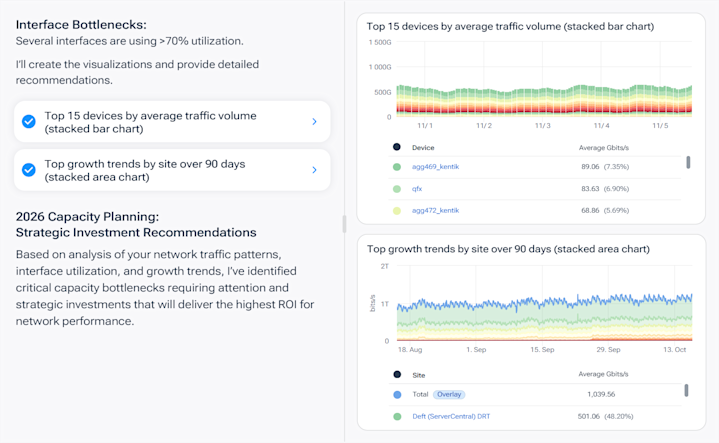
Design traffic and network architecture with confidence
- Identify opportunities to reduce or optimize cost with utilization trends and recommendations.
- Automate analysis workflows to inform precise, cost-effective decisions and guide smart investments.
- Get help with planning for future demands with capacity, runout, and cost forecasts.
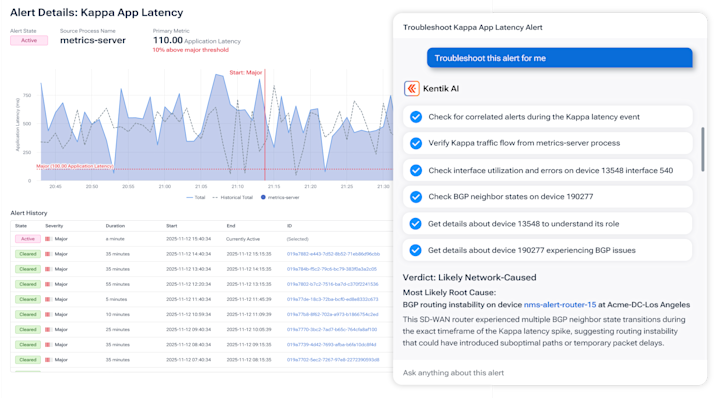
Operate faster and smarter with accelerated workflows
- Accelerate troubleshooting with advanced reasoning and automated data analysis to lower MTTR.
- Data-backed recommendations provide easy validation.
- Codify institutional knowledge for repeatable process with natural language runbooks.
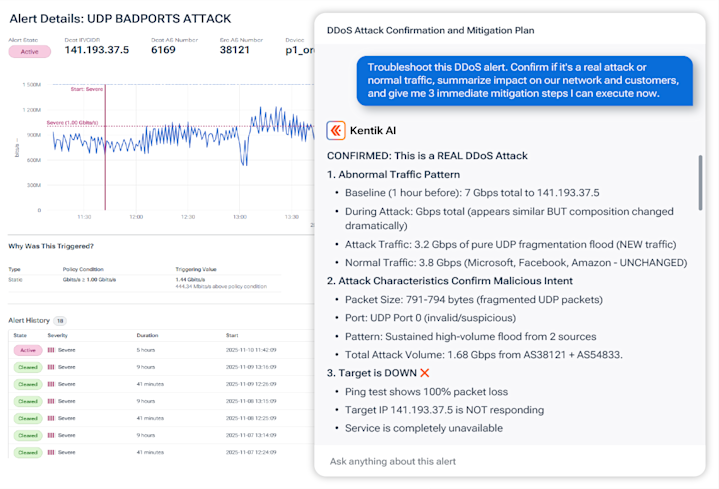
Protect network reliability and resilience
- Easily distinguish between legitimate and malicious traffic to catch and mitigate DDoS threats.
- Assess business impact to accelerate decision-making during an attack.
- Clear, explainable recommendations for mitigation protects uptime and customer trust.

“Kentik AI Advisor has proven to be a great new asset for our teams…it helped to drastically reduce our time and effort to mitigate outbound attacks.”
AI Advisor FAQs
How can I prioritize incident response using AI-driven insights?
Prioritize incidents by likely scope and business impact, not by raw alert volume: rank what is affecting critical services or the largest user segments first, then provide evidence that explains what changed and where to look. Kentik supports this by using AI Advisor to summarize incidents and guide investigation with telemetry-backed analysis so responders can focus on the highest-impact issues immediately.
How can I track network changes and correlate them with incidents?
Track change by pairing alerting/insights with time-window comparisons across your telemetry. Kentik supports this by letting you compare network traffic and performance before/after a change in Data Explorer and by using AI-guided investigations that help connect “what changed” to “what broke.”
How can I combine AI with telemetry for faster incident triage?
Combine AI with telemetry by using natural-language investigation to pull the right evidence across flows, device metrics, routing, and synthetics, then having the system summarize the likely drivers and next steps for validation. Kentik supports this by using AI Advisor for guided investigations and by connecting answers to real network telemetry so teams move from “something is wrong” to a defensible cause faster.
What tools provide AI summarization of network incidents?
Look for tools that generate incident summaries directly from telemetry and keep the logic auditable. Kentik AI Advisor can produce concise, actionable summaries tied to the underlying flow/metrics/synthetics data, so teams can validate conclusions and accelerate communication and remediation.
How can I reduce mean time to detect and mean time to resolve network incidents?
Reduce MTTD by baselining normal behavior and alerting on meaningful deviations quickly, and reduce MTTR by shortening the “figure out what changed” step with automated comparisons and guided investigation. Kentik supports this by pairing real-time telemetry with AI Advisor and automated change triage so engineers can isolate drivers faster, validate hypotheses with data, and confirm fixes without dashboard hopping. See also: Cause Analysis).
Related reading about AI Advisor and AI observability
Learn more about AI in networking and Kentik AI in our articles about:


