Security in an SD-WAN World

Summary
As one of 2017’s hottest networking technologies, SD-WAN is generating a lot of buzz, including at last week’s Cisco Live. But as enterprises rely on SD-WAN to enable Internet-connected services — thereby bypassing Carrier MPLS charges — they face unfamiliar challenges related to the security and availability of remote sites. In this post we take a look at these new threats and how Kentik Detect helps protect against and respond to attacks.
Protecting Availability for Internet-based WAN Sites

For enterprises, SD-WAN makes a lot of sense. Carrier MPLS services are really expensive bandwidth. Enterprises have historically paid those high prices to get SLA guarantees. But the reality is that within most providers both MPLS VPN services and public Internet services ride on the same shared network infrastructure. Enterprises are starting to realize this and looking to save some money by switching to public Internet circuits as a transport mechanism.
SD-WAN products enable this shift by using overlay tunnels on top of underlying Internet links. According to Gartner analyst Andrew Lerner in his June, 2017 blog post “SD-WAN is going Mainstream” there are an estimated 6000+ paying SD-WAN customers and 4000+ production deployments. Unfortunately, like most things in IT, this journey is not without challenges.
One thing that needs to be carefully considered is the security ramifications of moving from a private MPLS circuit to a public Internet circuit. The first aspect that comes to mind is privacy of the data. Now that the traffic is routing over the Internet, encryption becomes a must have. Most organizations have some sort of data that has be carefully guarded whether it is HIPPA, PCI, or any other compliance rules they are dealing with. This can be fairly easily solved with a firewall or SD-WAN appliance that creates IPSec tunnels between the sites.
Another important consideration is the possibility of DDoS attacks, which become a real concern once your office locations are on public IP addresses. E-commerce websites have been dealing with this for years but most enterprise WAN sites were spared due to the private IP routing they were using on MPLS VPN services.
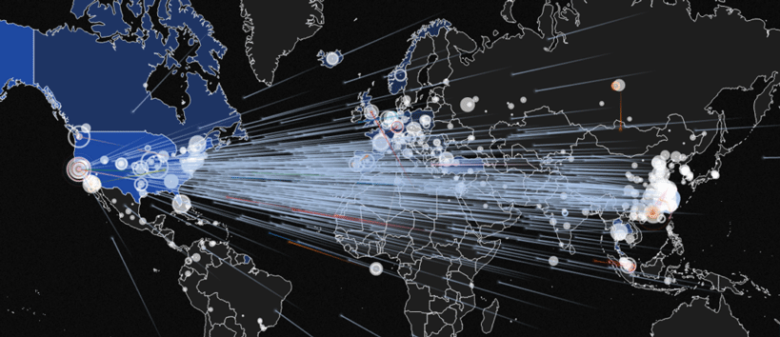
For a lot of enterprises, the risk of having a remote site taken off the network by a DDoS attack is simply unacceptable. That’s definitely true if it’s a customer service office, and becomes critically so when you’re talking about retail locations that generate revenue. With voice and data services being combined to ride over the same circuit, that type of attack would mean the employees in that remote office cannot get their work done or the cash registers stop raking in the dough.
Thankfully Kentik Detect can help here. Our flexible and powerful alerting policies give network managers very granular visibility into attacks when they take place, and our anomaly detection system can send users proactive alert notifications whenever current traffic deviates noticeably from the historical pattern. We also offer a number of automated mitigation options. One option is to use the power of BGP to announce a Remote Trigger BlackHole (RTBH) route from our portal to the routers in your network. If the IP address under attack is blocked, however, this may complete the attack by taking the site offline. So we’ve also partnered with A10 and Radware to create bi-directional API integrations with their orchestration and scrubbing solutions to mitigate DDoS attacks. This allows the attack traffic to be scrubbed out while clean traffic continues to flow to the remote office.
If you’re rolling out SD-WAN and haven’t thought about a comprehensive way to understand end-to-end traffic, as well as to detect and stop DDoS attacks, take a look at how Kentik Detect can help. Learn more about our big data-powered network traffic intelligence, dig into our industry-leading DDoS detection, take a look at our integrations with Radware and A10 and explore how we can help monitor network performance. Or, if you’re ready to dive right in, you can request a demo or start a free, fully functional 30 day trial.
